As the Manjaro kernel boots up the machine, its Network Manager automatically connects to the DHCP server via the enabled network interface. It then provides the client with the IP address, subnet mask, lease time, DNS server, gateway, and other details.
If the machine works as an Apache server, it must be easily accessible to the clients via a static IP address. Besides, as a precaution, users also have to protect the machine from unnecessary access from outside the network. This demands the need to set the network interfaces manually via Manjaro Network Manager or through commands and configuration files.
In this article, we learn to configure the network interface via GUI and CLI manually. We also simplify the Unrestricted Firewall (ufw) configuration process for new users as a precautionary step after Manjaro installation.
Setting Up Network Interface
Manual network interface setting includes assigning the machine with an IP address, gateway, DNS server locations, routes, and subnet mask. It is done via Manjaro NewtrokManager and CLI.
Getting Started
Before getting started with the manual network configuration, the system needs to meet certain conditions:
- enabled network interfaces
- the ethernet cable is connected
- the interface has an IP address
- the routing table is all set
- the device can reach the system inside or outside the local network
- the hostname-to-address resolution works fine
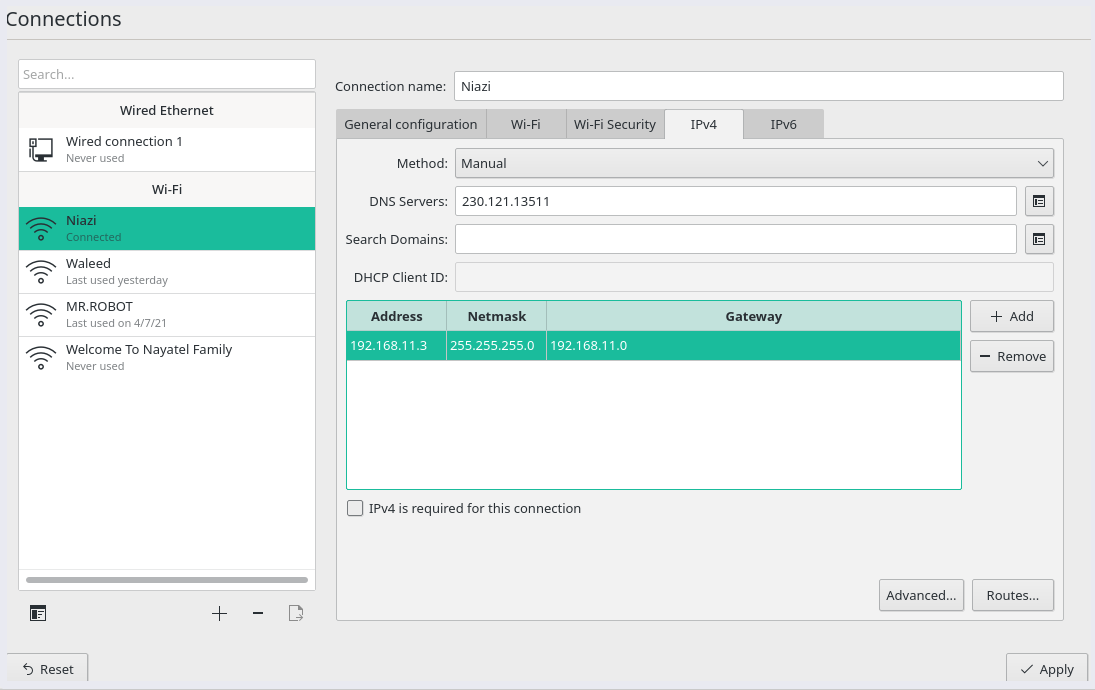
Static IP Setting via GUI
Search for the “Connections” inside the Manjaro application launcher. Inside the network connection menu, select the current network settings to edit/configure the connection.
Select the current connection and choose the IPv4 settings tab.
Select ‘Manual‘ from the ‘Method‘ drop-down menu for Static IP, and click on ‘Add‘ to fill in the address, subnet mask, gateway, and DNS server details. Lastly, click on ‘Apply‘ to restart the network with new settings.
Static IP Address Aliases
The GUI also allows to set up a number of addresses for a single interface. It’s possible by clicking on a ‘+’ sign or ‘Add’ button on the same screen to add a new IP address. Here are few details about address aliases:
- Each alias address requires a netmask but not gateway details.
- The save option greyed out without valid information.
- It does not need to be on the same netmask, even though it listens to traffic on the same physical network.
Use the following command to display the working interface with the two Ip addresses.
Static IP Setting via CLI
Another way to configure Static IP is via systemd. For Manjaro network interfaces, custom routes are configured inside /etc/systemd/network/ directory. The configuration files for each interface are identified based on the interface name. Hence, the file for network interface enp0s3 will be /etc/systemd/network/enp0s3.network.
Make sure to disable the NetworkManager, as it overwrites the manual settings.
Create or edit the above network interface file with root privileges. Here’s an example file:
[Match]
Name=enp0s3
[Network]
Address=192.168.11.0/24
Gateway=192.168.11.1
DNS=152.234.15.8
DNS=215.158.11.10
Now enable and start the network service.
To revert to the DHCP settings, delete the above file and restart the NetworkManager.
Setting Up Firewall with UFW in Manjaro
A functioning firewall is a critical part of any secure Linux system. By default, all Linux distributions come with an installed firewall configuration tool known as Uncomplicated Firewall (ufw). UFW is an interface for iptables and is designed to simplify the firewall configuration task.
According to the ufw man page, the tool does not provide full-fledged firewall functionality via CLI. Instead, it’s to ease the process of addition or removal of simple rules. Also, ufw aims to provide host-based firewalls.
To get started with securing the network, install ufw if not available:
Setting ufw Default Policies
Since we are getting started with the ufw configuration. By default, ufw is disabled. Check ufw status by typing the following command:
Execute the following command to enable ufw settings.
Enabling ufw will initiate the firewall default policy. That is, ufw only permits outgoing connections and denies all the incoming connections. In other words, the Manjaro server is not accessible from outside the network. While user applications can connect to the outside world.
If disabled, we can set the rules to execute ufw default policies.
manjaro@manjaro:~$ sudo ufw default allow outgoing
To enable the default policies, edit the /etc/default/ufw file. Note that the firewall settings will automatically initiate whenever the system reboots. These rules are sufficient to protect a personal Manjaro OS. However, a Manjaro server must respond to incoming requests.
Enable SSH Connections for Manjaro Server
The above setting denies all incoming connections. To allow legitimate SSH or HTTP connection to the Manjaro server requires creating rules in ufw. This setting will enable the user to connect and manage the server via a secure shell connection.
The above command is equivalent to setting a rule for a connection via an ssh port 22. Hence, UFW is aware of the ports utilized by the application protocols due to the services listed in the /etc/services file.
However, we need to specify an appropriate port if the SSH daemon listens to a different port. For instance, if the server listens on port 3333, use the following command to set the ufw rule:
UFW Configuration for IPv6
UFW supports IPv6 settings to manage firewall rules along with IPv4. To do that, edit the ufw configuration file in the /etc/default directory and following settings:
Now ufw is configured to add and manage policies for both IPv4 and IPv6.
Other Connections
ufw allows users to manage various subnet rules, specific IP addresses, port ranges, and network interfaces.
To specify port ranges:
To specify subnet with a specific destination port:
To set rule for specific IP address
Additionally, it also allows creating rules to deny connections from IP addresses and services. All it requires is to replace allow with the deny command.
Conclusion
This article summarizes Manjaro’s manual network interface and firewall configuration settings for beginners. We discussed setting a static IP address via GUI and commands/configuration files. Moreover, the article also demonstrates setting the default Unrestricted Firewall (ufw) to allow limited access to the machine from users across the internet.