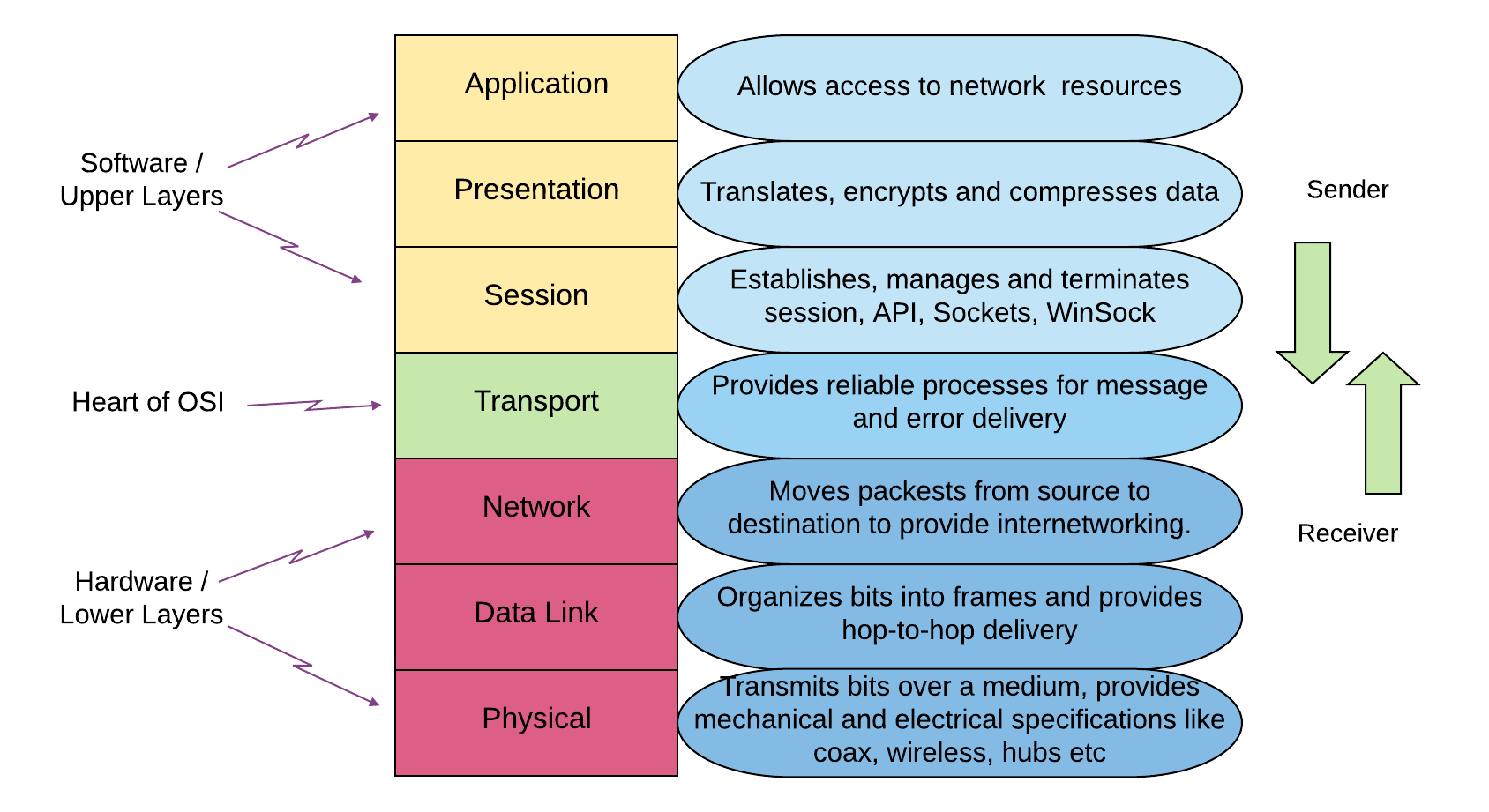
The Open System Interconnection (OSI) model conceptually illustrates seven abstraction layers of communication framework that devices use for interoperability over the network. In the 1980s, the model was a globally accepted standard framework for network communication.
The model defines a set of rules and regulations required to render interoperability between different software and devices.
It was introduced by the Internet Organisation of Standards in 1984 when computer networking was only becoming a new concept. Even though the internet these days is based on a simpler networking model, TCP/IP. The OSI 7-layer model is still used to visualize the basic essential networking architecture and troubleshoot problems.
7 Layers of OSI Model
The OSI model is divided into seven layers to represent network architecture. Each layer performs its own set of tasks and communicates with the layers above and below it to carry out successful network transmission. Let us discuss all of the layers and their properties in a ‘top down’ manner.
7. Application Layer
It is the only layer that involves direct interaction with the data from the end-user. In other words, this layer provides human-computer interaction, such that the web browsers or email clients applications rely on it to ensure communication. Hence, the applications rely on the layer to use its protocol and data manipulation services to transmit useful information. Some of the most common application layer protocols are HTTP, SMTP (enables email communication), FTP, DNS, etc.
6. Presentation Layer
This layer prepares the data for the application layer by considering that the software application accepts and requires encoding, encryption, formatting, or semantics. It gets the incoming data from the layer below it and translates it into an application-understandable syntax. Hence, it prepares the data and makes it presentable to be rightfully consumed by the application layer. It also receives data from the application layer and compresses it to transmit over the session layer. The compression process minimizes data size that optimizes the efficiency and speed of data transmission.
5. Session Layer
As the name suggests, the session layer is responsible for creating a communication channel between devices called a session. This layer keeps the communication channel open long enough for successful and uninterrupted data exchange. Eventually after complete transmission, it terminates the session to avoid resource wastage.
The session layer offers checkpoints to synchronize data transfer as well. This way, the layer can resume session transmission from certain checkpoints, if paused or interrupted in between, instead of transmitting entirely from scratch. It is also responsible for authentication as well as reconnection.
4. Transport Layer
The fourth layer of the OSI model is responsible for end-to-end communication. It receives data from the session layer, breaks it up into smaller bits at the transmitting end called segments, and sends it to the network layer. The transport layer is also responsible for sequencing and reassembling segments at the receiving end.
At the sender’s end, it is also responsible to ensure flow and error control for data transmission. Flow control determines the optimal required speed for communication so that a transmitter with a stable and faster connection does not overflow the receiver with a relatively slower connection. It makes sure that data is sent correctly and completely through error control. If not, it requests retransmission.
3. Network Layer
The network layer is responsible for receiving segments from the transport layer and dividing them into even smaller units called packets. These packets are then reassembled at the receiving device. The network layer delivers data to their intended destinations based on the addresses found inside these packets.
It performs logical addressing to find the best possible physical route to transmit the packet. At this layer, routers play a very vital role as it uniquely identifies each device on the network. The process is called routing.
2. Data Link Layer
The Data Link layer does the job of maintaining and terminating communication between two physically connected nodes. It splits down the packets obtained from source to frames before sending them to the destination. This layer is responsible for intra-network communication.
The data link layer has two sub-layers. The first being Media Access Control (MAC) renders control flow using MAC addresses and multiplexes for device transmissions across a network. The Logical Link Control (LLC) undertakes error control, identifies protocol lines, and synchronizes the frames.
Physical Layer
The lowest layer of this model is the physical layer. The layer is responsible for optically transmitting data between connected devices. It transmits raw data in the form of bitstreams from the physical layer of the sender device to the physical layer of the receiver device by defining bit transmission rate. Hence, it performs bit synchronization and bit rate control. Since it is called the ‘physical’ layer, it involves physical resources such as cabling, network modems or hubs, repeaters or adapters, etc.
Advantages of OSI Model
- The most vital role that the OSI model plays is to lay the foundation of basic network architecture, provide visualization and better understanding.
- It helps network operators to understand the hardware and software required to build a network on their own.
- It comprehends and manages the process performed by the components across a network.
- Allows ease in troubleshooting issues by pinpointing the layer that has been causing problems. Helps administrators to resolve them accordingly without interfering with the rest of the layers in the stack.
Conclusion
Open System Interconnection OSI model is a reference model that provides a convenient representation of data transmitted across a network. It splits the network communication tasks into seven manageable bits performed on each abstract layer. Each layer has a unique responsibility entirely independent of the other layers of the model. Where some of the layers handle application-related functionalities, the rest of them cope with data transportation responsibilities. Hence, it distributes jobs into quick and convenient layers and is considered the architectural model of computer networks.