Installation and Simple Vulnerability Windows Scanning
[adthrive-in-post-video-player video-id=”YsE8Prl6″ upload-date=”2020-09-14T14:59:31.000Z” name=”Installing Nessus on the Kali Linux” description=”Installing Nessus on the Kali Linux” player-type=”collapse” override-embed=”true”]
What is Nessus? Nessus is a tool for vulnerability assessment, and it is a paid tool. In this article, we will discuss the free version of Nessus known as Nessus Essentials, which is also called Nessus Home. It has limited features and quite handy to carry out the vulnerability scanning automatically.
Nessus has a lot of interesting features. Some of them are listed below:
- It has a nice GUI, which is easy for use.
- The scan can be done easily and more quickly. Also, it is easy to set up the scan.
- It will generate a report that is formatted nicely, and the resulting output will be organized and neat.
In this article, we will see how to execute a simple windows vulnerability scan and to set up the Nessus essentials. For this purpose, we will use the 32-bit Kali Linux on VM.
Instructions to install
The following steps are to be followed to install the Nessus on the kali Linux for a 32-bit operating system. For a different operating system, similar steps should be followed.
1. For registration, click on the link below:
https://www.tenable.com/products/nessus/nessus-essentials
Once the link is open, enter your first and last name with an email address. This is done to get an activation code after registration.
2. Choosing the Right Version: In the next step, select the appropriate version for the operating system and press the download button.
3. License Agreement: Now, agree with the terms of condition and the license agreement to save it on your system.
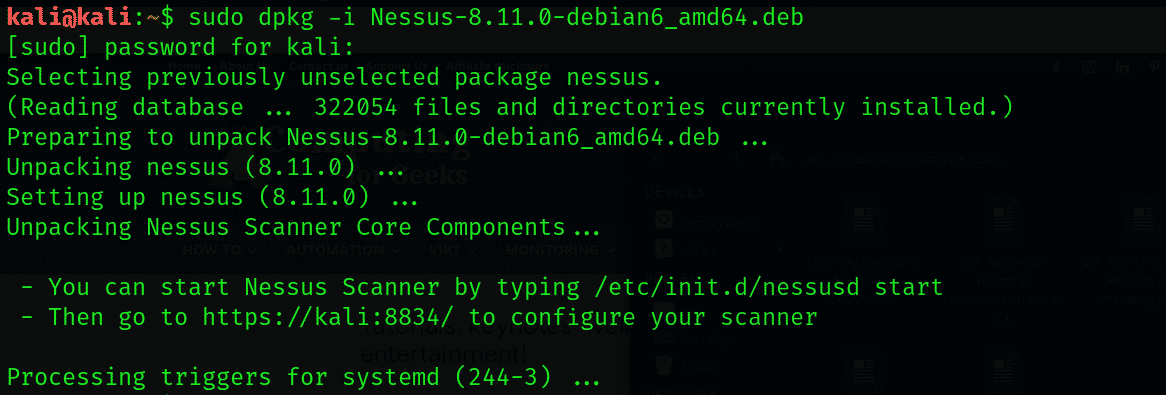
4. Unpacking Nessus: Now unpack the Nessus by going to the download directory through terminal.
5. Begin the Nessus daemon with the help of the following command:
It can also be done during the boot time by the command:
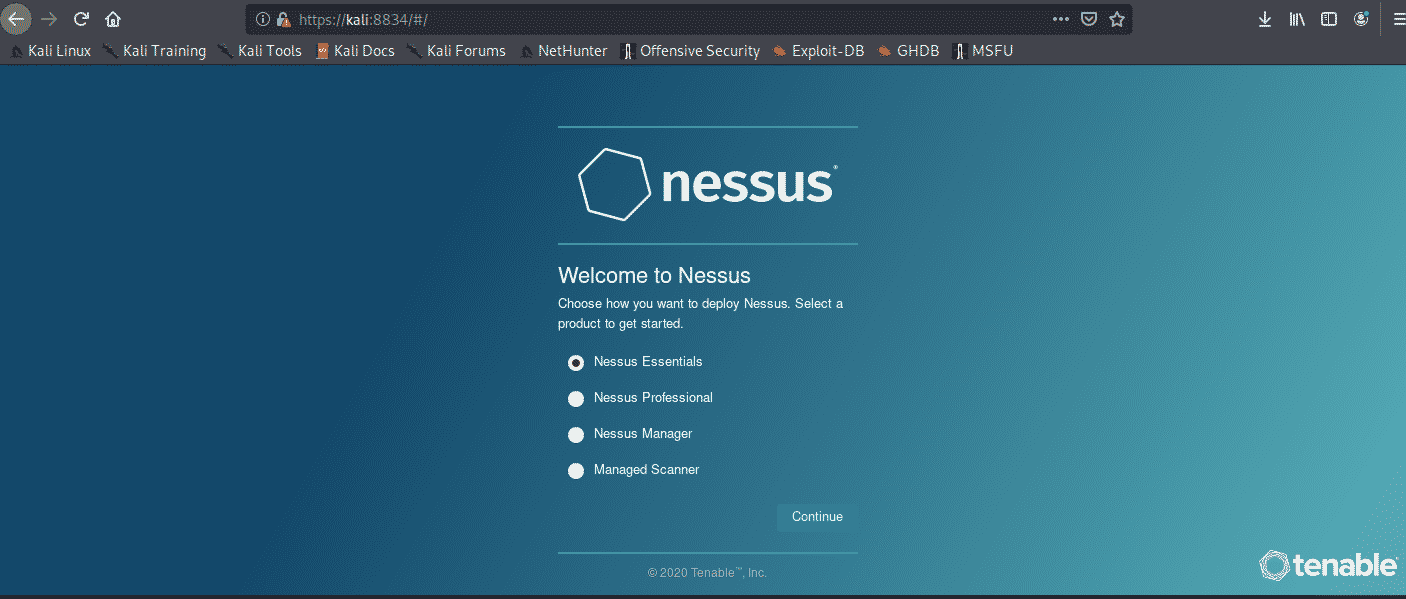
6. Security error and allow Nessus: A security error will have occurred when we browse the GUI Nessus using this link.
To allow Nessus, click on Advanced, then on Add Exception, and finally on Confirm Security.
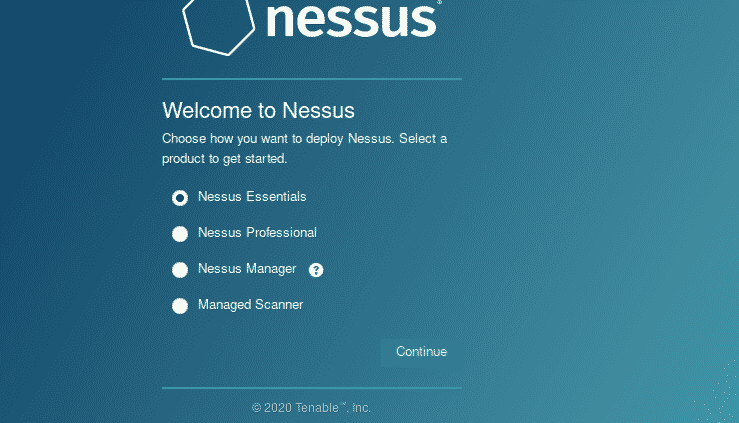
7. Selecting Nessus Essentials: Select it and press Continue.
8. Skipping the Activation Code Registration
9. Entering the Activation Code: An email will be received. Go to your inbox and copy the activation code to paste it in Nessus. Then press continue.
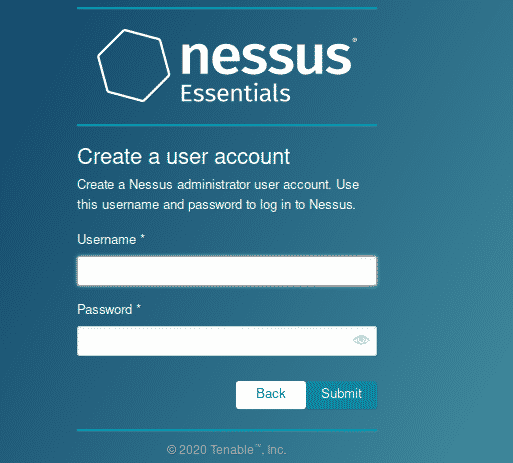
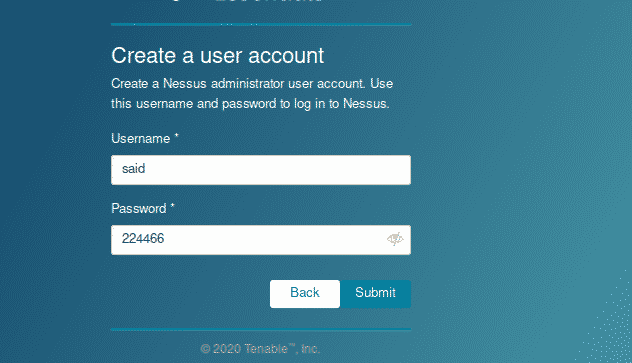
10. Creating a User Account; Now create the user account by giving the details and submit it. This account is used to login to the Nessus.
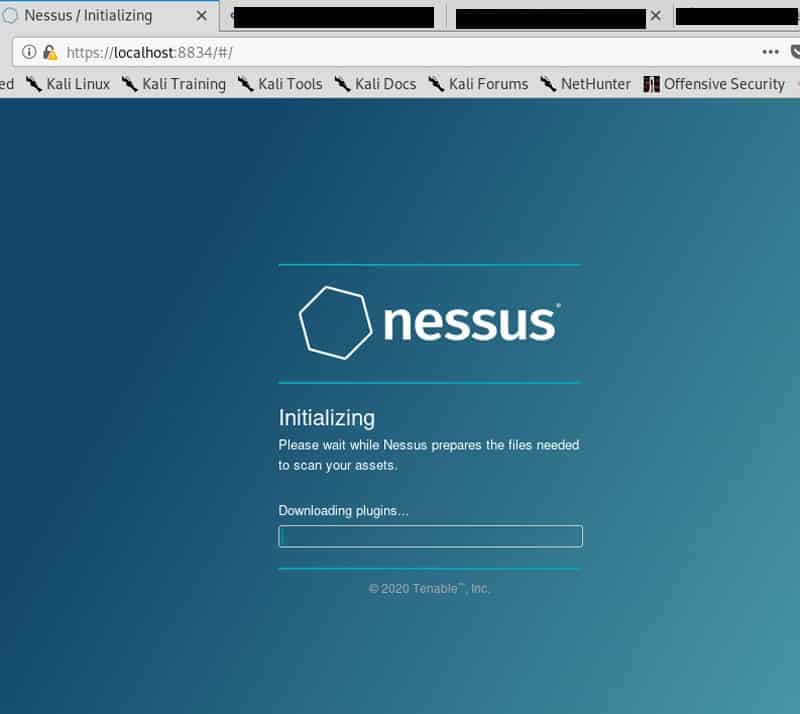
11. Patience: Here, wait for 45-60 minutes until the Nessus finish its installation. Some times it will take a longer time to install.
Create a new custom policy
By performing a simple Windows Vulnerability Scan, we will try out some features after installing the Nessus. It is based on scan policies that include what to look for or not.
First of all, change the policies from the sidebar. Then press on New policy. The Nessus show a lot of predefined policies. We can also create policy according to the user with the help of scratch, which can be customized according to the need of the user. Then click on the Advanced Scan. Now give the name to policy and a short description.
Different drop-down menus are shown on the left side. Click on the discovery; we see different options of setting in the host discovery. To scan arrange of hosts or network, uncheck the option Test the local Nessus host. This option will not allow Nessus to scan, and only the host with single windows will be scanned. Now keep the default settings and leave as it is.
In the next step, we will go to the section of port scanning. Here we see that the SYN option is active by default while the TCP option is not active. This is because the Nessus will use the quick SYN scan then the normal TCP scan. Furthermore, the UDP option can be enabled, but it takes a longer time, and it is not effective.
We will also see more setting options for vulnerability scanning. There is also the tab of credentials where we enter the login details to allow the various protocols such as SSH and SNMP to carry out the authenticate scan.
Now, go to the Plugin tab. They are like separate modules to carry out the vulnerability assessment of various components.
Plugins are also available for different types of Linux, web servers, DNS, firewalls, and FTP, etc. To make vulnerability assessment more accurate and perfect, mix the variety of plugins. It is necessary to select the right plugins to avoid the scanning of irrelevant vulnerabilities like cisco vulnerabilities on a Linux target.
As here, we are scanning the normal host of windows 7. To do this, click the option disable all and go with the Windows: Microsoft Bulletins option. For exploring more about plugins. Now go on a specific plugin by clicking on it. After doing that, a popup will appear that contains the descriptions, solutions, and risk ratings. After configuring the settings, click to save it.
Conclusion:
In this article, I have shown you how to install Nessus software tool in Kali Linux. I have also explained how this tool works and its usage.