[adthrive-in-post-video-player video-id=”TkDfgRRH” upload-date=”2020-07-07T13:45:50.000Z” name=”Top stress tools in Kali Linux 2020.1″ description=”Top stress tools in Kali Linux 2020.1″ player-type=”collapse” override-embed=”true”]
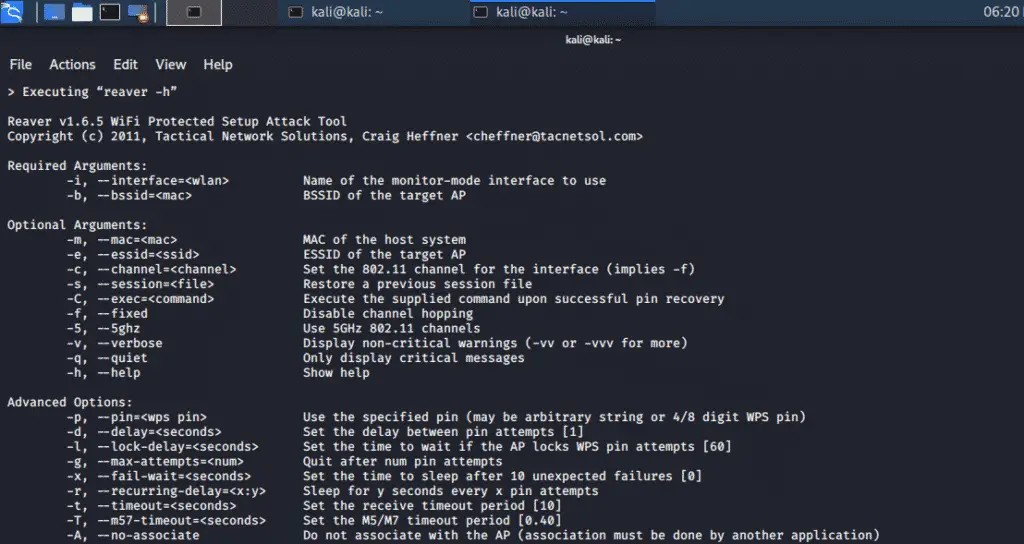
Reaver tool:
To recover WPA / WPA2 passphrases, Reaver adopts a brute force against Wifi Protected Setup (WPS) registrar PINs. Reaver is built to be a reliable and effective WPS attack tool and is tested against a broad range of access points and WPS frameworks.
Reaver can recover the desired Access point WPA/WPA2 secured password in 4-10 hours, depending on the Access Point. But in actual practice, this time might be reduced to half.
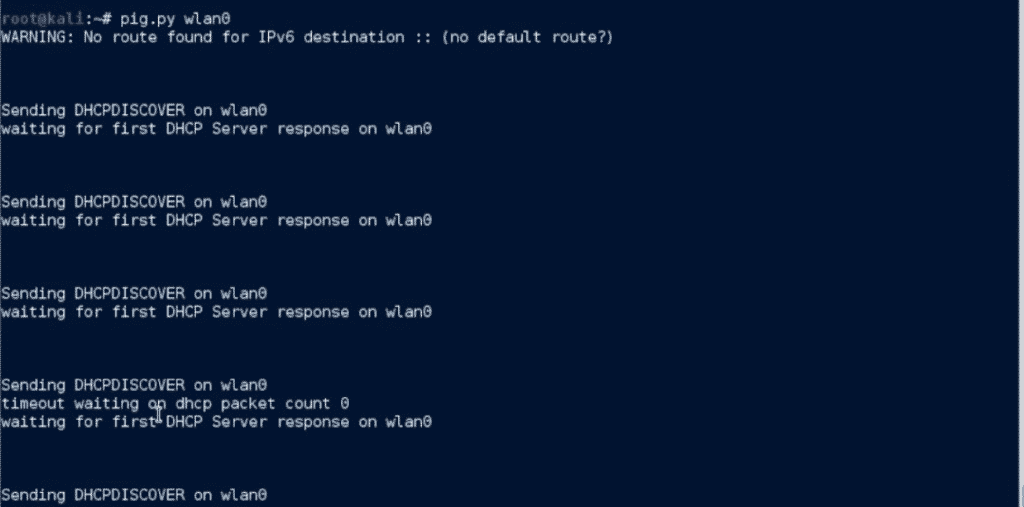
DHCPig:
This Python tool attacks a DHCP server with an advanced exhaustion attack that consumes all the IP addresses on a LAN network. This attack stops new clients from gaining access to the IPs and stops them from using existing IPs. It sends the Gratuitous address resolution protocol (ARP) to all windows hosts and gets them offline from the network. DHCPig needs the scapy 2.1 library and root privileges to operate. This tool is tested on various DHCP servers for windows and has successfully passed.
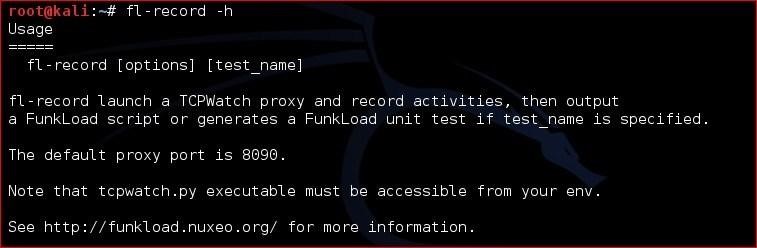
Funkload:
Funkload is a Python toolkit that works as a load web-tester that perform various operations on a server. It works as a functional testing tool for regression testing of web projects. It also helps in determining bottlenecks in a server by loading a web application through performance testing, and the results are displayed as a detailed report of performance measurement. The load testing tool in the funkload toolkit operates to identify bugs that cannot be exposed using volume or longevity testing. The stress testing tool is used to engulf the resources of web applications and tests whether the application can be recovered or not.
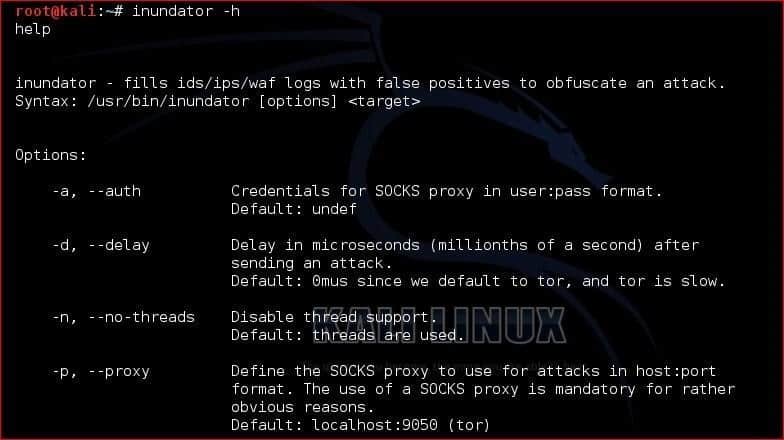
Inundator:
This tool is used to detect unidentified intrusions using false positive generators that support several targets. Inundator is a queue driven and multithreaded package for fast and quick performance. It requires SOCKS proxy and authentication details for the SOCKS server. It can target a single host, multiple hosts, and multiple subnets in a network.
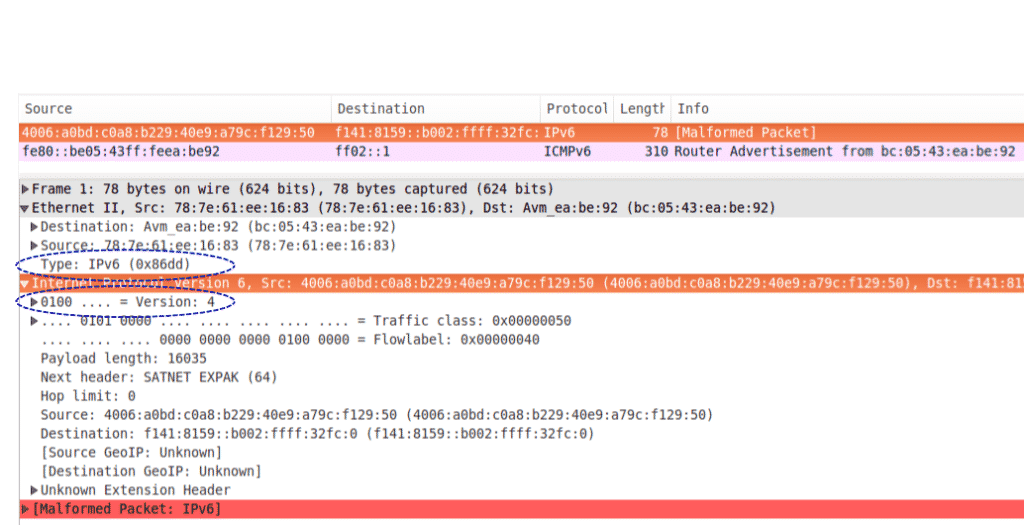
Ipv6-toolkit:
The ipv6-toolkit contains several security evaluation tools for ipv6 and also perform troubleshooting of networks. It can perform attacks on IPv6 devices to test their resiliency and also troubleshoots network-related issues. This toolkit has many tools that work with packet crafting, neighbor discovery data packets, and scanning tool.
It has an addr6 tool for analyzing IPv6 address, flow6 for security evaluation of IPv6, frag6 for fragment-based attacks. The icmp6, jumbo6 are used to work on error related messages. The na6, ni6, ns6 are used for operation on neighbor’s discovery packets. The ra6, rd6, and rs6 works on IPv6 router related messages. The scan6 is a scanning tool, while the tcp6 tool launches various TCP-based attacks.
Termineter:
It is a python language tool that gives out a platform for testing the security of smart meters. It uses the c12.18 and c12.19 network protocol for communication between source and target. It implements 7-bit character sets via ANSI type 2 optical probe with a serial interface to work with Smart Meters.
THC-SSL-DOS:
This tool validates and checks an SSL connection’s performance. When securing an SSL connection on a server machine, it needs 15x processing power than on the client machine. So, for this purpose, the THC-SSL-DOS tool exploits the server’s asymmetric overloading and disable it from the internet. This exploit is extensively used, and it also affects the SSL secure Renegotiation feature through-provoking more than a thousand renegotiations with the help of a single TCP connection.
Conclusion:
These stress tools are very important for security professionals, as they provide the best security evaluation of servers. Some of these stress tools are pre-installed in Kali Linux, while others can be downloaded from Git repository and Kali tools repository.