ParrotSec has provided the answer to the question in the form of a program called Anonsurf – “Dance like no one’s watching.”
Anonsurf is a script made by the development team at ParrotSec, which included Lorenzo Faletra (@palinuro), Lisetta Ferrero (@sheireen) and Francesco Bonanno (@mibofra), and that is maintained by Nong Hoang Tu (@dmknght). This script was made to provide users with system-wide anonymization. In simpler words, anything you do while you have Anonsurf started on your system would be nearly untraceable. Anonsurf not only routes all your traffic through Tor, but it also lets you start i2p services and clear any traces left on the user disk. Anonsurf also kills away all dangerous applications by virtue of the Pandora bomb, so you do not need to worry about having a Tor browser and other scripts running to hide your system. The best part is that all this is contained in a simple start/stop function.
Anonsurf uses Tor IPTables for the configuration of IP packet filter rules. While Tor provides a browser solution, Anonsurf is capable of much more.
If the above paragraphs do not make sense to you yet, do not panic. It is very easy to use Anonsurf and we are here to guide you through to anonymity.
Anonsurf was also made available for Kali Linux, though the pictures in this article were taken on Parrot OS.
This article will show you how to run Anonsurf’s Anon Mode.
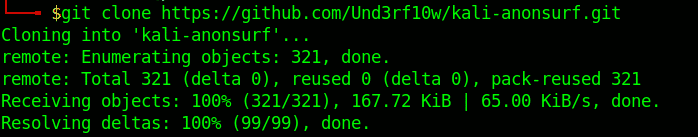
Step 1. Clone
You can clone Anonsurf and other integrated repos from GitHub using the command below. This repo was forked from ParrotSec. Und3rf10w has made some improvisations, like using DNS servers of Private Internet access. Plus, it already contains the Pandora package.
It will normally take a few moments to get this module downloaded, depending upon your internet connection. The following screen should appear after the download is complete:
Step 2. Install
First, find the downloaded folder “kali-anonsurf.”
Give the installer execute permissions.
Run the installer with ./installer.sh.
This adds keys, updates, and installs anonsurf for you.
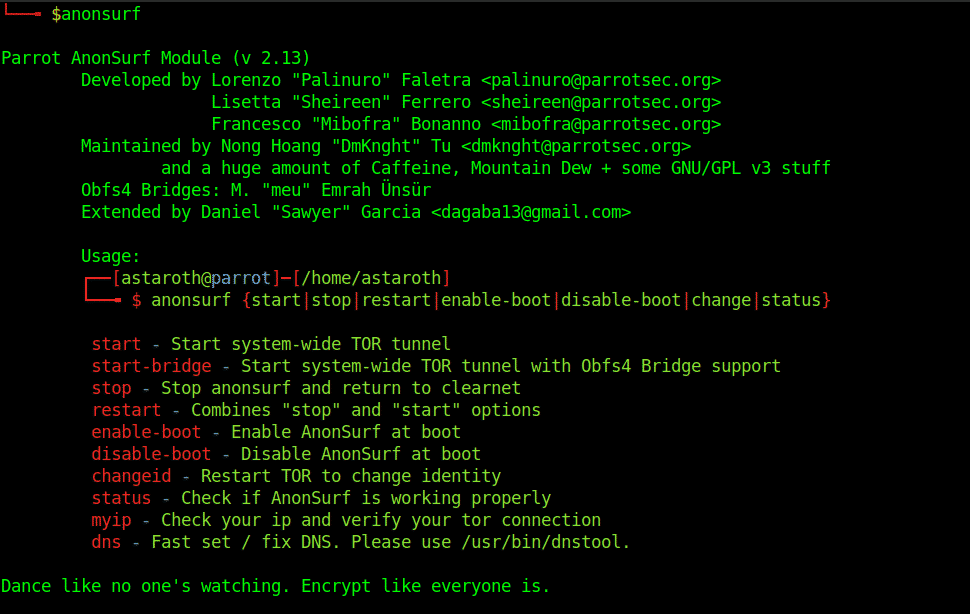
The installation process can take a few minutes, after which you should be able to go completely anonymous with a single command. To check whether the installation is successful, enter the following command:
The following screen will appear if you have correctly gone through the installation process:
Step 3. Go Anonymous
Now that you have a working Anonsurf module, the following simple commands will help get you started.
- start starts the anon mode
- stop finishes the anon session
- restart combines “stop” and “start” options
- start-bridge starts system-wide Tor tunnel with Obfs4 bridge support
- changeid restarts Tor to change identity
- enable-boot enables Anonsurf at boot
- Also by $ systemctl enable anonsurf
- disable-boot disables Anonsurf at boot
- Also by $ systemctl disable anonsurf
- status checks whether Anonsurf is working properly
- Uses the Nyx application to display information about Tor service, bandwidth, nodes, etc.
- myip checks your IP and verifies your Tor connection
- dns replaces your DNS with the OpenNIC DNS servers.
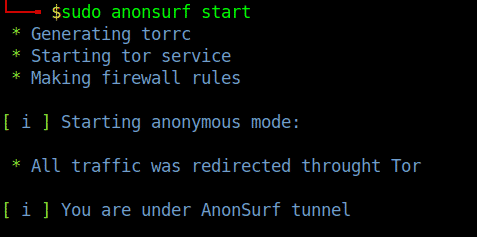
Run the following command from the terminal to launch a secure Tor channel to direct your traffic, which will change your IP every five to ten minutes
Yes, it is that simple. Be sure that you are running this command as the root user or using the sudo prefix. However, if you are a Parrot OS user, you can simply select the ‘start service’ option to anonymize your browsing immediately.
The program may prompt for a restart of various applications to clean out dangerous caches.
To check your IP at any given time, enter the following command:
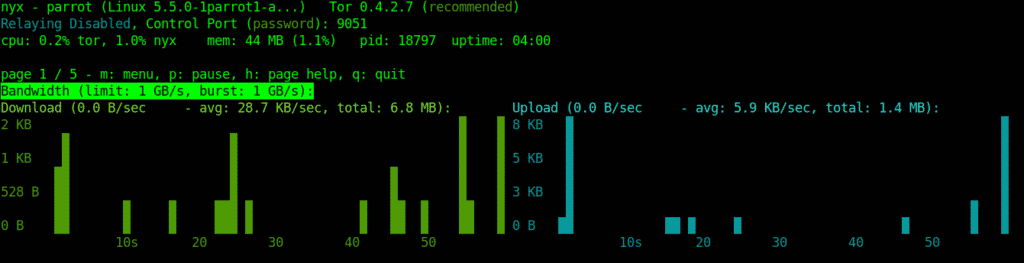
To check the status of the module, enter the following command:
Nyx shows us information about the Tor service, bandwidth, and other information, such as nodes, average speed, etc.
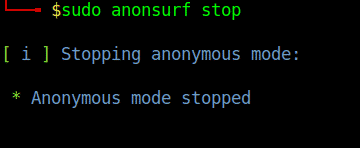
A simple stop command ends the session and wipes clean any traces.
It is as simple as that!
Cessation
The use of VPNs and TOR will help you spoof or hide your IP address. Scripts like MAC changer allow users to spoof their Mac, too. The use of such tools in conjunction could bring you to your own optimized solution. The inclusion of i2p services in the tool covers both the circuit-based routing of Tor and the packet-based routing of i2p. Plus, these functions run in the background, so even if you kill the terminal, the sessions will continue. Anonsurf anonymizes the framework to a very good extent but does not give you a total incognito state.
However, there are a few weaknesses to Anonsurf, as well. As it follows the Tor protocols for routing and is encrypted by each hop, Anonsurf makes browsing a comparatively slower option than VPNs. It all depends on whether you prioritize anonymity or speed. Moreover, Anonsurf does not work in some countries, such as Egypt. People have been using solutions like Tor, Proxy-chains, and VPNs for some time, now. Still, no other tool is more complete of a solution than Aanonsurf.
There is no such thing as complete anonymization or a 100% secure channel yet, as there is no tool that is both easy to use and manage and fully secure. As you may have noticed, you do not have to be a professional to be able to use Anonsurf. This tool will work the same wonders for a beginner as for a professional.
You may have heard people say, “Privacy matters.” It sure does on the Internet!
Disclaimer
Anonsurf uses Tor services that may be deemed illegal to use in your country. Please keep up with your country’s laws and avoid doing anything that is illegal or not allowed. This article is for educational purposes only, and hence it is the responsibility of the reader to be responsible, use the information for lawful purposes, and avoid using the program for anything that may be harmful to them or others.