After reading this tutorial, you will be able to open ports easily in specific Linux distributions and a universal way to open them in all distributions.
Firewalls described in this document include Nftables, UFW (Debian/Ubuntu) and Iptables.
Every step explained in this article contains screenshots, making it easy for every Linux user to implement them.
Note: Make sure the services for open ports are active.”
How to Open Ports Using Nftables
Nftables is the Iptables replacement. Today Nftables became more important than the discontinued Iptables firewall.
New distribution versions like Debian already bring Nftables.
You still can use Iptables and its frontend UFW (Uncomplicated Firewall), which simplifies all tasks. Both of them are also explained in this tutorial after this section dedicated to Nftables.
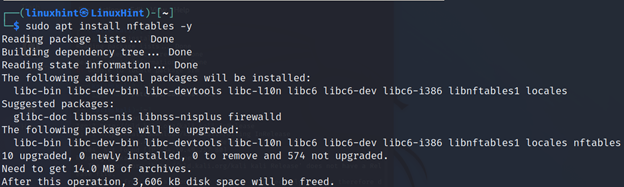
To begin, make sure Nftables and all dependencies are installed. On Debian-based Linux distributions, run the command shown in the screenshot below.
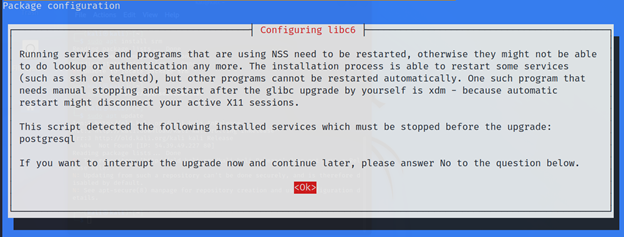
During the installation process, you will be requested for confirmation to restart some programs and services. Press ENTER.
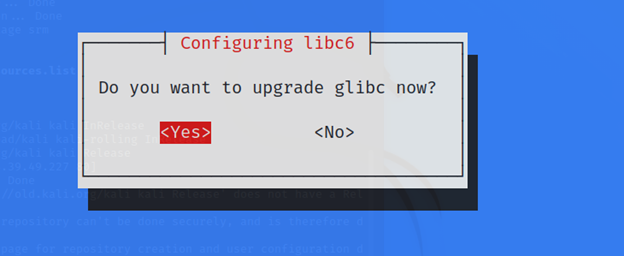
In case they are updated for your glib library, press YES if asked to upgrade it.
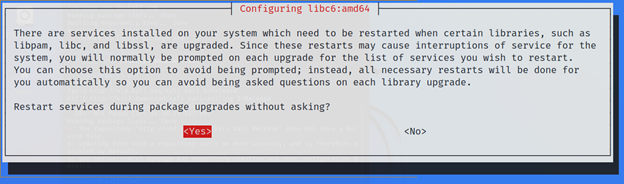
When asked if restart services again, press ENTER.
Once Nftables is installed, you can start writing your firewall and defining ports to remain open.
Below you can see a simple Nftables firewall with a restrictive policy, dropping all traffic except for the defined open ports 80, 443, 53 and 22. All executable lines are explained in the comments.
define LinuxHintNet = 192.168.0.0/16
define AllowPorts = {80,443,53,22}
#I declare a new table containing chains and rules. I named this table #"Restrictive"; the name is arbitrary. The "inet" applies rules to both #IPv4 and IPv6. For IPv6 only use "ip6" or use “ip” IPv4.
add table inet Restrictive
# Once the table was defined below, I added three chains, Incoming, Redirect and Outgoing. Their names are also arbitrary. All of them drop incoming, outgoing and forwarding traffic as the default policy.
add chain inet Restrictive Incoming { type filter hook input priority 0; policy drop; }
add chain inet Restrictive Redirect { type filter hook forward priority 0; policy drop; }
add chain inet Restrictive Outgoing { type filter hook output priority 0; policy drop; }
# Below, added two rules allowing loopback traffic.
add rule inet Restrictive Incoming iifname lo counter accept
add rule inet Restrictive Incoming oifname lo counter accept
# I also added rules to allowing traffic through the ports I defined in the #AllowPorts variable.
add rule inet Restrictive Incoming tcp sport $AllowPorts counter accept
add rule inet Restrictive Outgoing tcp dport $AllowPorts counter accept
add rule inet Restrictive Incoming udp sport $AllowPorts counter accept
add rule inet Restrictive Outgoing udp dport $AllowPorts counter accept
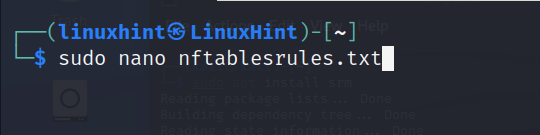
Below you can see a screenshot of the firewall.
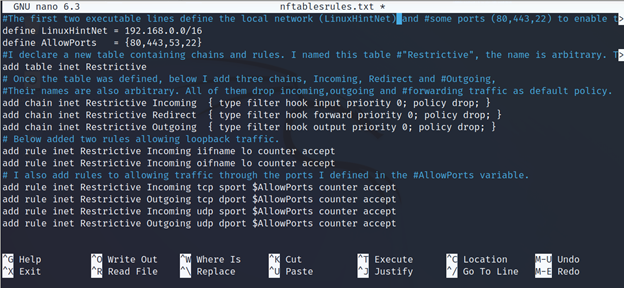
After saving the file, execute the firewall using the following command, where “nftablesrules.txt” must be replaced with the file name you created.
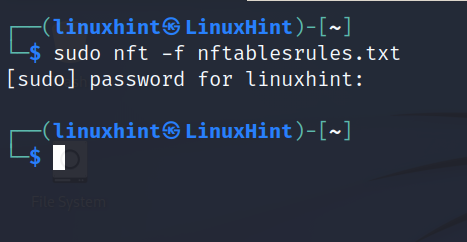
To see the active firewall rules run:
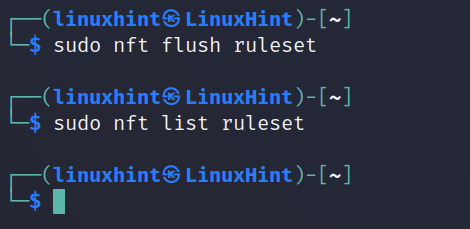
If you want to flush your firewall rules, run the command shown below.
Now, let’s explore the most simple option with UFW.
How to Open Ports With UFW (Uncomplicated Firewall)
This section explains how to open ports in Debian-based Linux distributions like Ubuntu using UFW (Uncomplicated Firewall), which, as its name suggests, is an easy-to-use Iptables frontend to create firewall rules, including these we need to open ports in Debian/Ubuntu Linux.
Note: To open ports, in addition to firewall rules, make sure the service you want to enable is active.
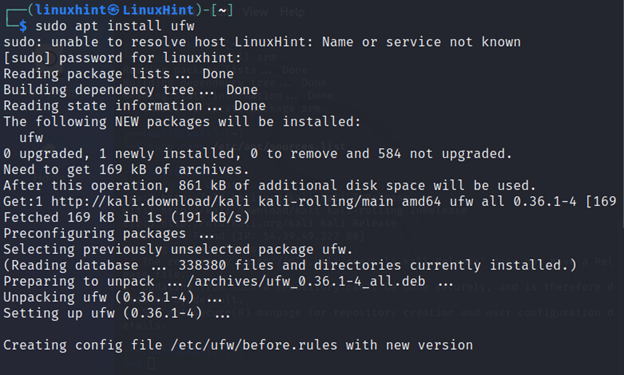
If UFW is not installed in your system, you can get it using the apt packages manager by running the following command.
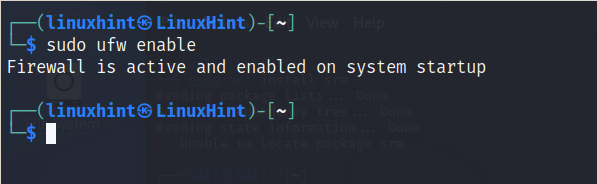
After installing UFW, you need to enable it by executing shown in the screenshot below.
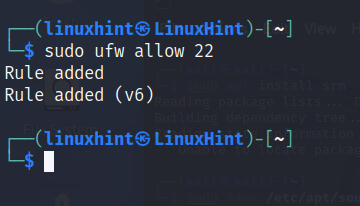
Once UFW is installed, you can open a port by specifying it, as shown below.
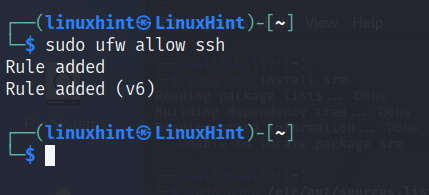
For example, to open port 22, run the following command.
You also can open a port by specifying the service or protocol instead of the port number, as shown in the image below.
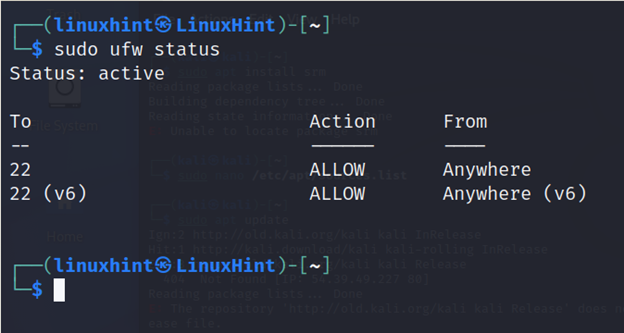
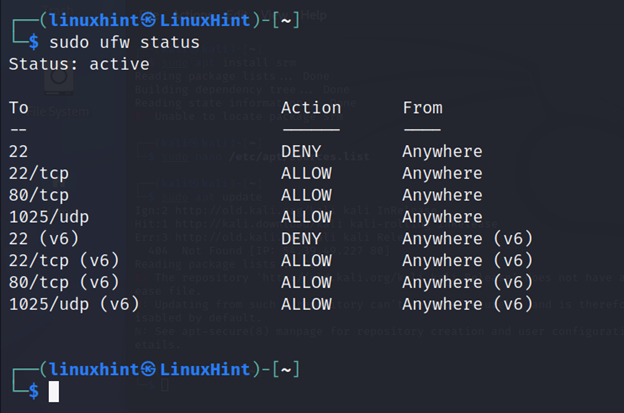
When adding a rule like the previous one, you can check if the port was successfully opened by running the following command.
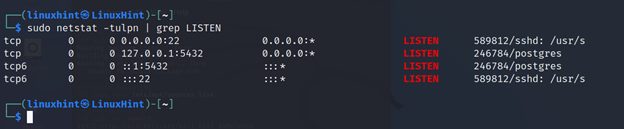
But even if the firewall allows traffic, you must check if the desired service is running and the port is open; you can execute the command shown below.
As you can see in the above image, the port is listening.
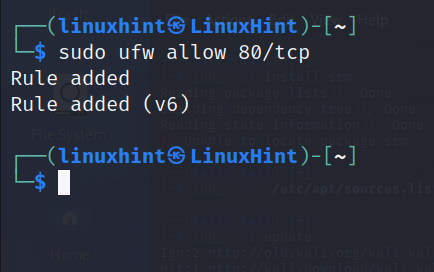
With UFW (And all firewalls), you can specify the protocol through which you allow traffic on a specific port. Just add a slash after the port number or service name followed by the protocol. In the example below, port 80 is on the TCP protocol.
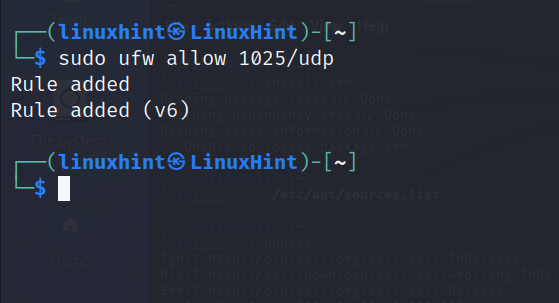
The following example allows UDP traffic through port 1025.
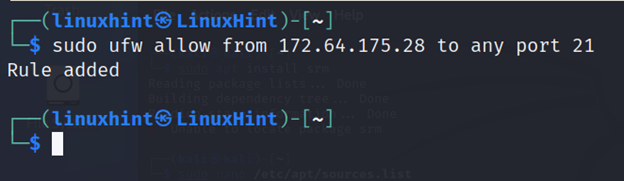
To allow traffic through a port from a specific IP address, use the following syntax, where the IP address and port number must be replaced with your desired IP/Port.
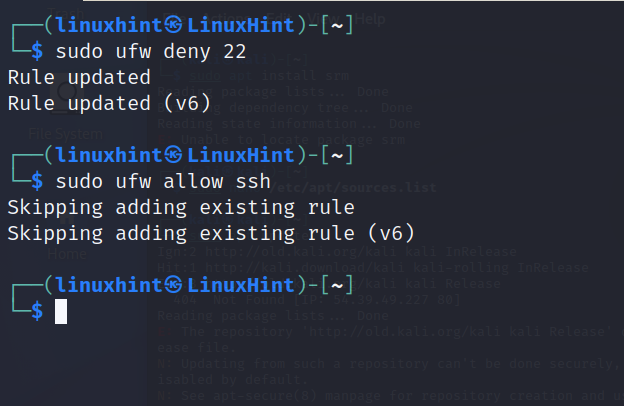
Note: To close a port using UFW, replace “allow” with “deny”, as shown below.
To close port 22, run:
Or
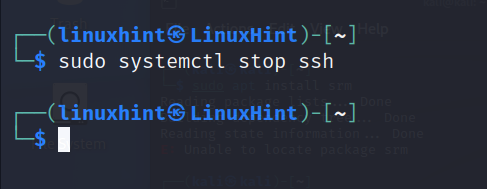
Note: To close port 22, make sure you disable the ssh service is disabled by running the command below.
Again, I check if my rules were properly added by running UFW followed by the status option.
That’s the easiest way to open ports in Linux.
Opening Ports in All Linux Distributions (Iptables)
This section shows how to open ports using Iptables, the firewall behind the previously explained UFW frontend.
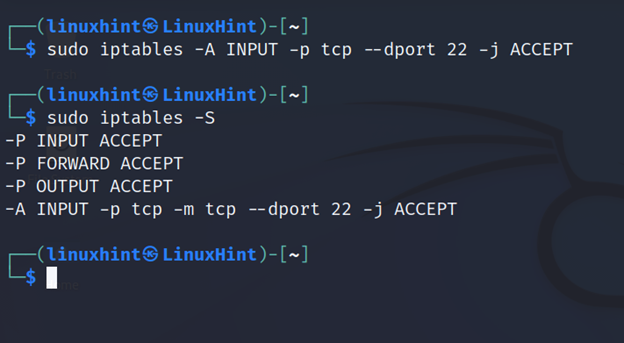
The following rule allows incoming (INPUT) TCP traffic through port 22. Replace “22” with the port number you need to open.
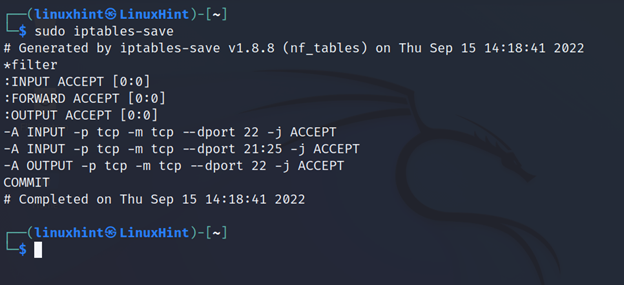
The sudo iptables -S command allows you to see active firewall rules. As you can see above, the added line is active.
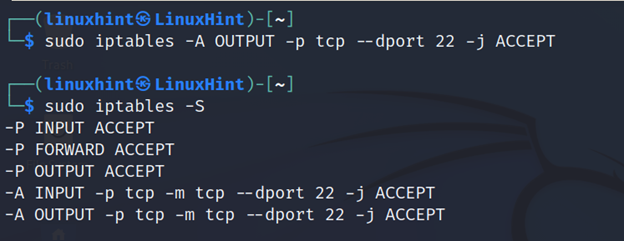
The following line allows outgoing (OUTPUT) traffic through port 22.
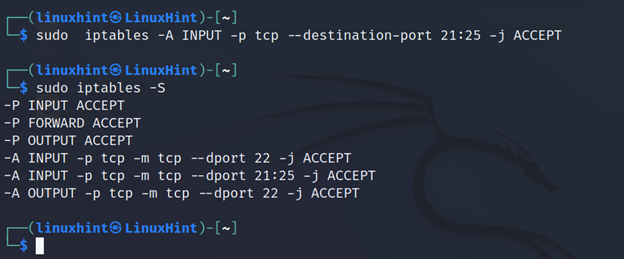
You can define a port range to open by implementing a colon between the starting and ending ports, as shown below.
To save the rules execute the command shown in the following figure.
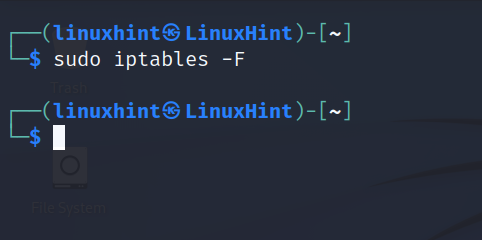
To flush Iptables rules, execute iptables followed by the -F (flush) flag.