This tutorial explains how to use the scp (Secure Copy) command to transfer files between computers.
The scp command is available on all Linux, Unix, and Windows systems. Its implementation will in all probability improve and ease the networking experience.
Security is provided by the ssh protocol.
This command allows us to transfer files reliably and securely from a computer to another. Together with the sftp command, also protected by the ssh protocol, scp is one of the most safe file transference techniques.
After reading this article, the reader will be able to easily share and fetch files with single commands.
All practical examples in this tutorial contain screenshots, making it easy for every Linux user to understand how commands are applied.
Requirements Before Using scp
The user will download files from or upload files to, it must have the ssh service running.
If the service is already running on the server, you can jump to the next section of this article.
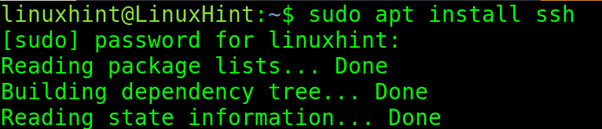
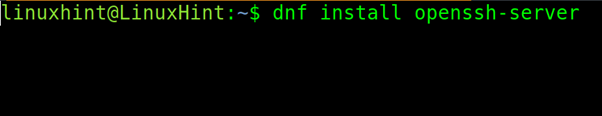
If the service isn’t running, the user can install it by following the instructions below for Debian and RedHat based Linux distributions.
On Debian based systems like Ubuntu, the ssh service can be installed with the apt packages manager as shown in the image below.
On RedHat based systems like CentOS, the ssh service can be installed by running the following command:
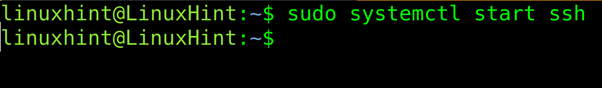
When the installation ends, on the server you want to connect to, start the service with the systemctl command as shown below (Debian based systems).
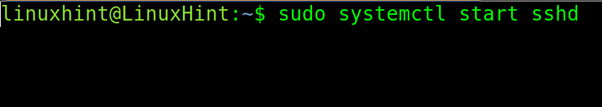
To start the ssh service on RedHat systems execute:
How to Download Files and Directories With scp (Secure Copy)
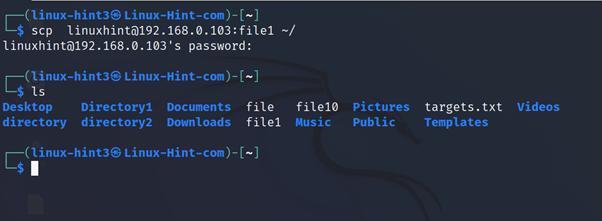
In the first practical example of this tutorial, a user downloads a file named <file1> to his home directory.
It is important to remember downloading or uploading files requires credentials of an existing user in the remote computer.
The syntax to download a file with scp is the following, where <Remote-User> is an existing user on the remote computer the user wants to download files from. <Server-IP> is the host or IP address of the server storing the file, <Path/To/File> is the path to the file to download and <Local-Directory> is the user’s computer local directory where the file is saved.
In the example below, the local user linux-hint3 logins as the linuxhint remote user in the server with IP address 192.168.0.103 and downloads a file named <file1> to his home directory. A post ls command execution shows file1 is locally present.
By default, after logging in, the remote current working directory is the remote user home directory.
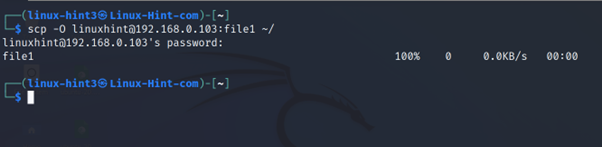
The -O flag is helpful to execute SCP legacy necessary to transfer files with systems which did not implement the sftp protocol.
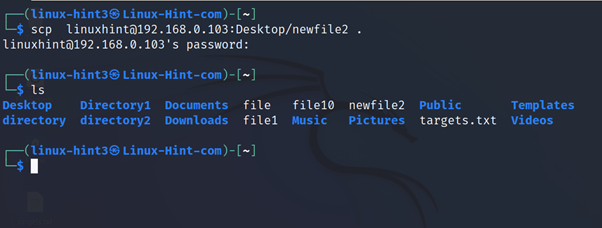
In the example below, the user downloads a file named newfile2, stored under the Desktop/ subdirectory. The file local destination is the current local directory represented by a period.
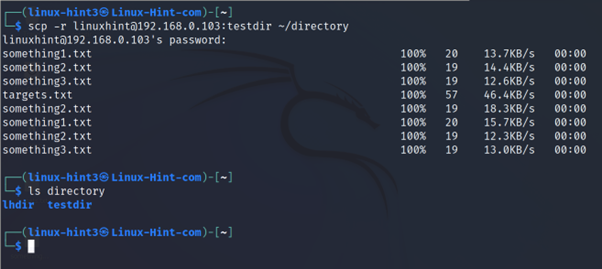
Downloading directories only requires adding the -r (Recursive) flag as shown in the screenshot below.
In the example below, the user downloads the remote directory named testdir/ to the local subdirectory named directory/.
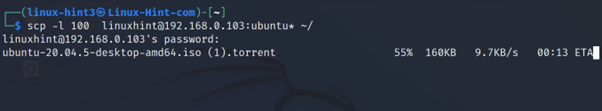
The -l flag allows limiting the download transference in Kb/s to control the bandwidth.
In the following screenshot, the user limits the bandwidth for the transference to 100 Kb/ps. As you can see, the user used a wildcard (*) to download all files whose name starts with “ubuntu”.
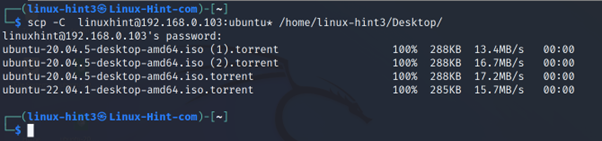
If the user wants to speed up the file transference, he can add the -C to compress files or directories during the transference, leaving the destination copy uncompressed (if the source was so).
In the example below, the user implements the -C (Compress) flag to download all files starting by “ubuntu” to the local Desktop/ subdirectory.
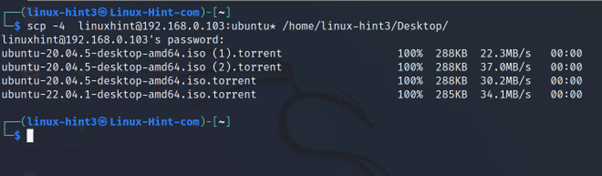
The -4 option forces the connection through IPv4 and the -6 option through IPv6.
In the next screenshot, the user forces the file transference through IPv4.
How to Upload Files and Directories With scp
This section explains how to upload files with single commands using scp.
The syntax to upload regular files to a remote system using sftp is the following:
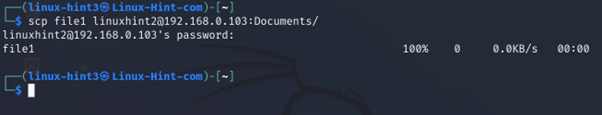
In the example below the user uploads a file named file1 to the remote subdirectory named Documents/.
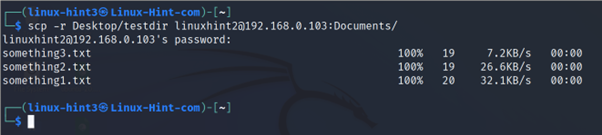
To upload directories, use the recursive -r flag, the rest of the syntax is similar to the examples described above.
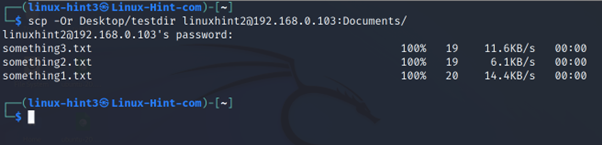
The -O flag is useful to upload files to systems without the sftp protocol.
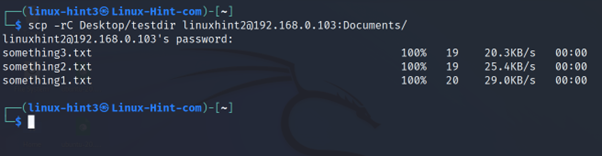
To speed up the transference, also when uploading files, the user can compress.
In the example below, the user combines the recursive -r flag with the -C (Compress flag).
Disabling scp Password Authentication and Enabling Key Authentication
Originally the scp protocol was based on the ssh (Secure Shell) protocol but currently it works through newer protocols like sftp or rsync.
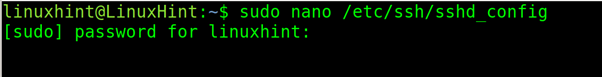
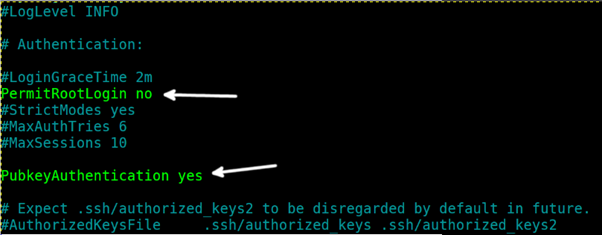
The configuration file to be edited to enable key authentication and disable password login is /etc/ssh/sshd_config. This file contains additional options to increase the scp files transference security.
On the computer, allowing incoming connections from where files are downloaded or where they are uploaded, open the /etc/ssh/sshd_config file with privileges using a plain text editor like vim or nano.
Scroll down and find the line containing PubkeyAuthentication no, replace it with PubkeyAuthentication yes (Replace the “no” with “yes”).
Also confirm PermitRootLogin no to disable root login because everyone in the world knows the existence of the root user, which may be the target of any type of attack including brute force.
The root superuser exists in all Unix based systems including Linux. It is not a good decision to allow login with a privileged username known by everyone in the world.
Don’t disable password login yet because the key copying process requires password login before systems are able to authenticate with keys.
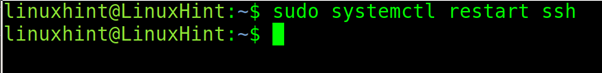
Exit the configuration file saving changes and restart the ssh service by following the instructions below.
Debian based Linux distributions:
RedHat based Linux distributions:
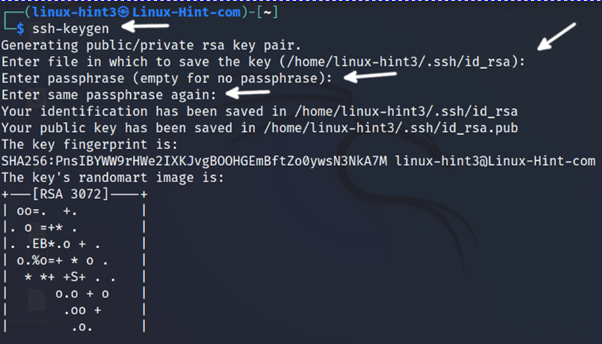
On the client side, the computer downloading and uploading files, the user must generate the keys pair with the ssh-keygen command.
After running the command, press ENTER to leave the default directory (~/.ssh/id_rsa) or the equivalent in your Linux distribution. The process allows the implementation of a passphrase to be required when authenticating. By including a passphrase, the security level is increased. It is recommended to type one and press ENTER. If you don’t want to add a passphrase just press ENTER without typing it.
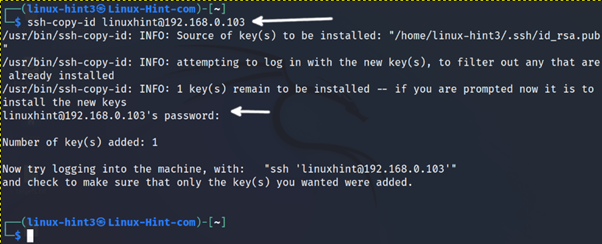
After successfully creating the keys pair, the client must send the key to the server using the ssh-copy-id command with the syntax of the following practical example.
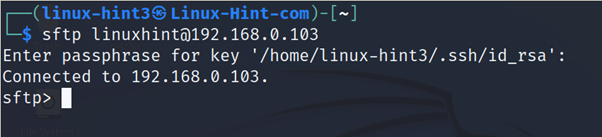
After copying the key, test the authentication method by connecting to the second device.
If the key authentication succeeds, the user will be able to login without typing the password. If the user has defined a passphrase when creating the keys pair, it will be requested instead of the password as shown in the screenshot below.
After confirming the public key authentication works properly, it is highly recommended to disable the password authentication.
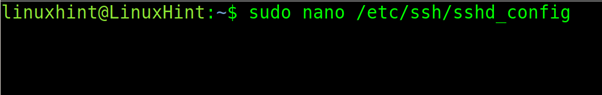
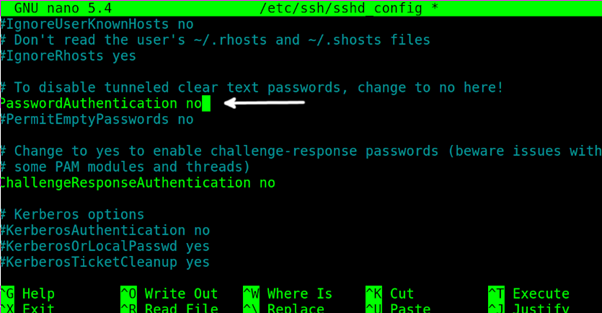
To disable the password authentication, on the server side, open the file /etc/ssh/sshd/config with privileges again using a text editor like nano or vi.
Scroll down the configuration file and replace the line PasswordAuthentication yes with PasswordAuthentication no.
In some cases, when the number of users is reduced, the scp/ssh port can be changed to prevent massive scans. This change must be done in this file. If the user changes the default port, he needs to implement the -p <Port> option when transferring files.
Exit saving changes.
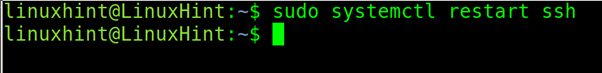
On Debian based Linux systems, restart the ssh service with the following command:
Restart the ssh service on RedHat based Linux distributions:
Now the user is able to login with key authentication.
Conclusion
Using the scp command is pretty easy. Every Linux user can learn it improving his experience with networking tasks. It definitively eases interacting with other computers within a network from the command line. All the instructions in this tutorial are valid for all Linux distributions except for the installation methods limited to Debian and RedHat based Linux distributions. Every network administrator working from the terminal must dominate this command.