TOR (The Onion Routers)
Tor (The Onion Routers) is a distributed network which is used for anonymity and privacy and is used by Activists, Hacktivists, Ethical Hacker, Black Hat Hackers and other people who want to hide their activities onlin. It is designed in a way that the IP Address of the client using TOR is hidden from server that client is visiting and the data and other details are hidden from client’s Internet Service Provider (ISP). TOR network uses hops to encrypt the data between client and server, and that’s why it provides better anonymity than a VPN. TOR network and TOR browser are pre-installed and configured in Parrot OS.
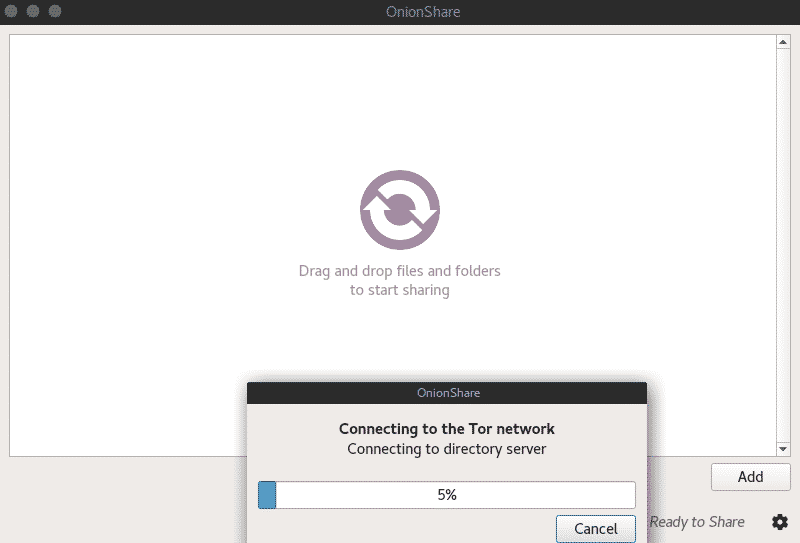
OnionShare
Onion Share is an open source utility which is used to share files of any size over the TOR network securely and anonymously. It is so secure and so simple to use, just drag your file and drop it to the OnionShare. It will then generate a long random URL which can be used by recipient to download the file over the TOR network using TOR browser.
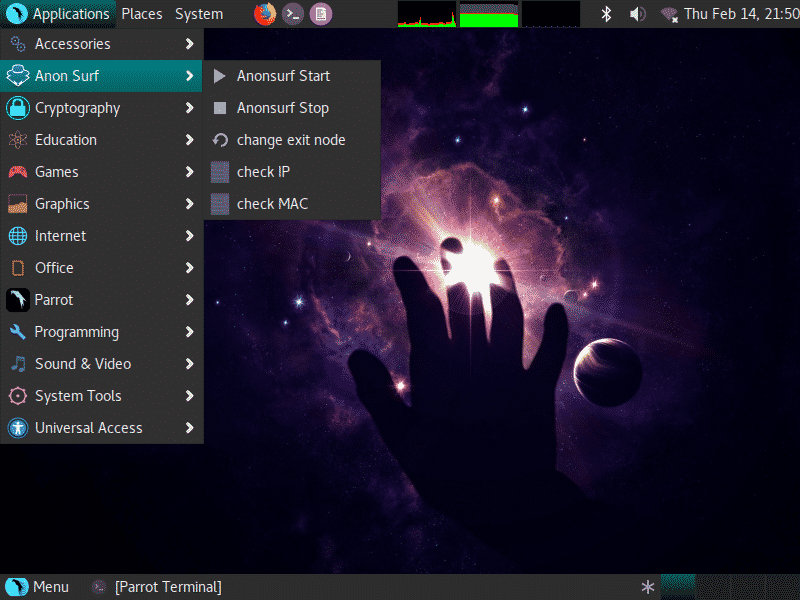
AnonSurf
Anonsurf is a utility that makes whole operating system communication to go over TOR, I2P or other anonymizing networks. You don’t need extra browser or anything for it. It doesn’t make only your browser communication secure but it also anonymizes your P2P communication and a lot of other communication protocols. You can start or restart anonsurf service from Parrot Sec menu, for CLI options
start - Start system-wide TOR tunnel
stop - Stop anonsurf and return to clearnet
restart - Combines "stop" and "start" options
changeid - Restart TOR to change identity
changemac - Change mac address
status - Check if AnonSurf is working properly
myip - Check your ip and verify your tor connection
mymac - Check your mac and verify your change mac address
changemac - Change your MAC ADDRESS (-r to restore)
Dance like no one's watching. Encrypt like everyone is.
I2P
I2P is another anonymizing network like TOR but it works in a little different way. It provides good anonymity & privacy on the internet and it can also be used to access darknet services.
console Launch in the current console.
start Start in the background as a daemon process.
stop Stop if running as a daemon or in another console.
graceful Stop gracefully, may take up to 11 minutes.
restart Stop if running and then start.
condrestart Restart only if already running.
status Query the current status.
install Install to start automatically when system boots.
remove Uninstall.
dump Request a Java thread dump if running.
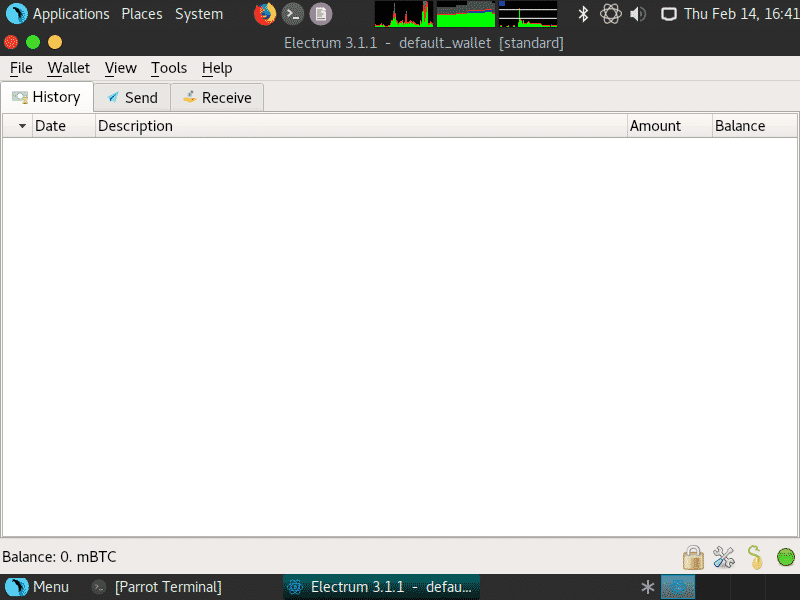
Electrum Bitcoin Wallet
Electrum Bitcoin Wallet is a wallet to keep and transfer your Bitcoin currency securely. It can sign transactions offline and then these transaction can be broadcasted online from another computer. It has distributed servers to keep your transactions anonymous.
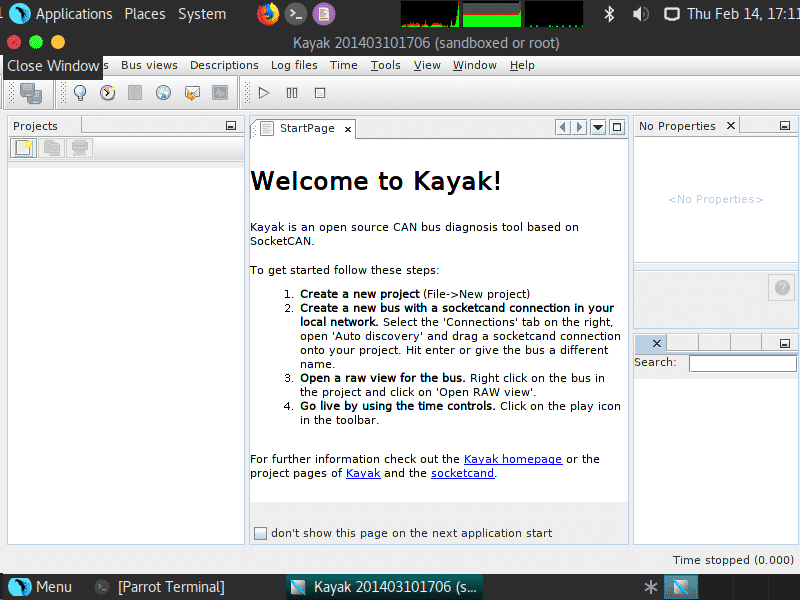
Kayak – The Car Hacking Tool
Parrot Security OS has a whole menu devoted for Automotive Pentesting tools, kayak is one of these amazing tools. It is a GUI tool based on Java to analyze CAN traffic. It has some cool modern features, such as GPS tracking, recording and playback capabilities.
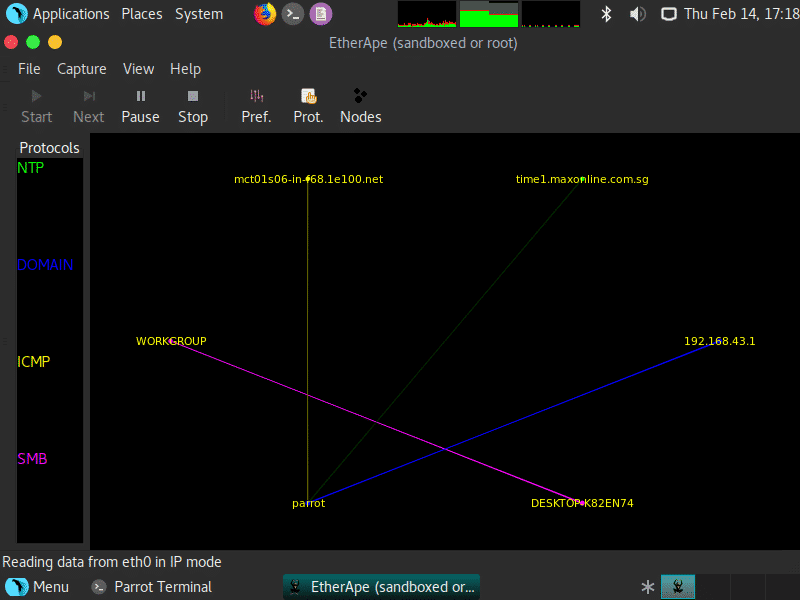
EtherApe
EtherApe is a GTK GUI based open source network sniffer and network analyzer. It display IP layer, link layer and protocol layer and uses different colors to differentiate the protocols.
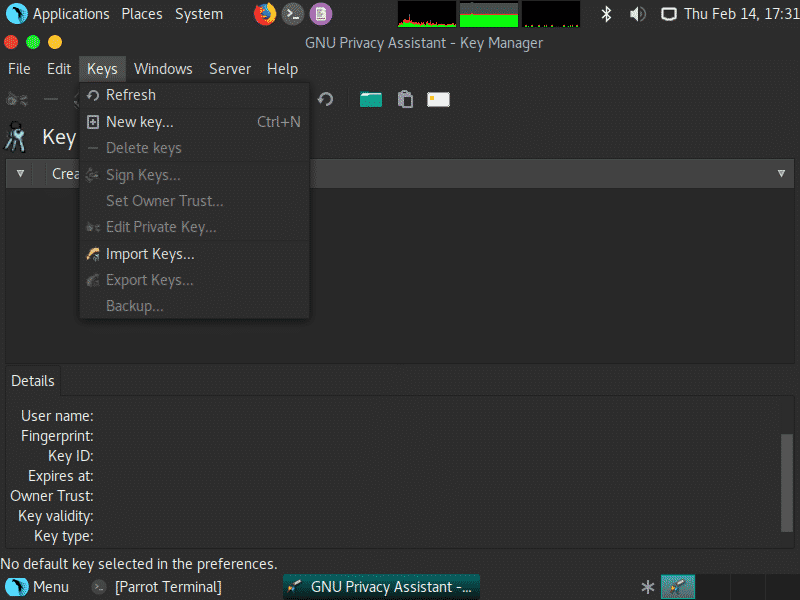
GPA – GNU Privacy Assistant
GPA is a GUI encryption software that makes the use of OpenPGP, a public key cryptography protocol to encrypt and decrypt files, documents and emails. It is also used to generate key pairs, storing them and to export the public keys.
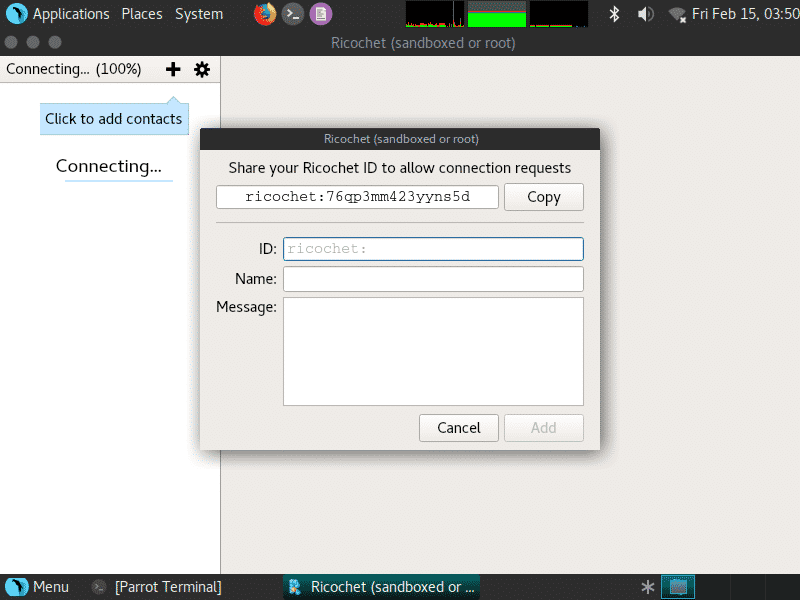
Ricochet
Ricochet is an anonymous and secure chat powered by TOR Network. Instead of usernames, it provides you with a long random string which looks something like ricochet:qs7ch34jsj24ogdf which is the address of the user. Messages sent using Ricochet are end to end encrypted and fully anonymous.
Nmap
Nmap (Network Mapper) is the most flexible and comprehensive tool used for port scanning and network security auditing. It is available in Parrot Security OS with Command Line and Graphical Interface which is called Zenmap. Usage example,
$ nmap hackme.org
Starting Nmap 7.70 ( https://nmap.org ) at 2019-02-15 09:32 EST
Nmap scan report for hackme.org (217.78.1.155)
Host is up (0.34s latency).
rDNS record for 217.78.1.155: cpanel55.fastsecurehost.com
Not shown: 963 filtered ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp closed ssh
25/tcp open smtp
53/tcp open domain
80/tcp open http
110/tcp open pop3
143/tcp open imap
...snip...
Nikto
Nikto is a powerful, free and Open Source Scanner which is used to identify common security loopholes in web servers. It scans Web Server’s version to check for version related problems. It also scans Web Server’s configurations such as HTTP allowed methods, default directories and files. Usage examples are
$ nikto -H # For help menu
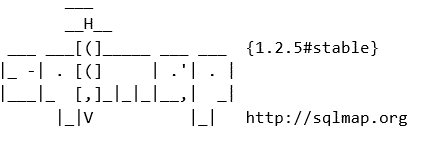
SQLMap
SQLMap is a powerful yet free penetration testing tool that is used to analyze vulnerabilities related to databases. It can automatically detect and exploit database vulnerabilities, also it can extract or manipulate the data from various types of databases. It automates the whole process of database pentesting and it can gather user infos, passwords and other details from the databases alone.
$ sqlmap --help
Options:
-h, --help Show basic help message and exit
-hh Show advanced help message and exit
--version Show program's version number and exit
-v VERBOSE Verbosity level: 0-6 (default 1)
Target:
At least one of these options has to be provided to define the
target(s)
-g GOOGLEDORK Process Google dork results as target URLs
...snip...
Crunch
Crunch is a dictionary maker for password attacks. It can generate wordlists according to your specifications and it will generate a dictionary with all permutations and combinations of letters, numbers and special characters.
crunch version 3.6
Crunch can create a wordlist based on criteria you specify. The output from crunch can be sent to the screen, file, or to another program.
where min and max are numbers
...snip...
CUPP
Custom User Password Profiler (CUPP) is an advanced dictionary generator for custom password profiling. It is better than crunch in a lot of ways, because it will prompt for some user data like username, birthdays, pet names and it’ll generate a wordlist automatically based on these specifications, so you won’t have to remember long syntaxes.
[ Options ]
-h You are looking at it baby! 🙂
For more help take a look in docs/README
Global configuration file is cupp.cfg
-i Interactive questions for user password profiling
-w Use this option to improve existing dictionary,
or WyD.pl output to make some pwnsauce
-l Download huge wordlists from repository
-a Parse default usernames and passwords directly from Alecto DB.
Project Alecto uses purified databases of Phenoelit and CIRT
which where merged and enhanced.
-v Version of the program
Metasploit Framework
Metasploit is a famous penetration testing and exploitation framework which is used to test for security vulnerabilities. It is built in Ruby language and supports Postgresql database for data management. It is has msfvenom which is used for exploit code generation and encoders to evade payload from antivirus solutions. To try Metasploit, type
Bleachbit
Bleachbit is a free disk space cleaner which is used to delete useless log files, internet history, cookies and temporary files. It has some advanced features like shredding files to prevent forensics and other data recovery techniques. It’s a complete all-in-one tool for permanently deleting your junk with no chance of forensics or recovery.
Macchanger
Macchanger is an awesome tool used to change interface’s MAC Address. It is used mostly to evade MAC filtering on routers and also to stay anonymous. Your device’s MAC Address is its identity, it can be used to locate you or to detect your on the internet, so it’d better be changed. To change your MAC Address, type
$ sudo macchanger -r wlan0
$ sudo ifconfig wlan0 up
Aircrack-ng
Aircrack-ng is a suite of tools used for Wireless Security Auditing or say WiFi cracking. It can be used to analyze, test, crack and attack Wireless Security Protocols like WEP, WPA, WPA2. Aircrack-ng is command line based tool and also has some third party GUI interfaces. Aircrack-ng has a lot of tools used for different purposes to attack the wireless network. It can be used to recover forgotten passwords.
OPENVAS
OpenVAS is free vulnerability scanner and it is a forked version of last free Nessus code on github after it was close sourced in 2005. For its plugins, it still uses the same NASL Language of Nessus. It’s a free, Open Source and powerful network vulnerability scanner.
If you are using OpenVAS for the first time then you need to auto-configure it using the following command. It’ll configure openvas service and generate a user and its password.
Netcat
Netcat is a raw TCP and UDP port writer and it can also be used as a port scanner. It’s an amazing tool which can be used to interact with any protocol like HTTP, SMTP, FTP, POP3 without using an application level software. It can connect to both TCP and UDP ports and also allows binding of an application.
To check for an open port, write
...snip...
hackme.org [217.78.1.155] 80 (http) open
To scan for a range of ports, type
(UNKNOWN) [127.0.0.1] 80 (http) open
(UNKNOWN) [127.0.0.1] 22 (ssh) open
CONCLUSION
With all these great tools, I am sure you will enjoy Parrot Security OS.