NOTE: Before getting started, ensure that the device you wish to connect to is online and the error is not a result of the device being unavailable.
Issue 1: SSH Service not Running
A common cause of SSH connection errors is the service not running on the remote host. This can be because of accidental service shutdown or service not starting after a system reboot.
To check if the SSH service is running, use the system manager using the command:
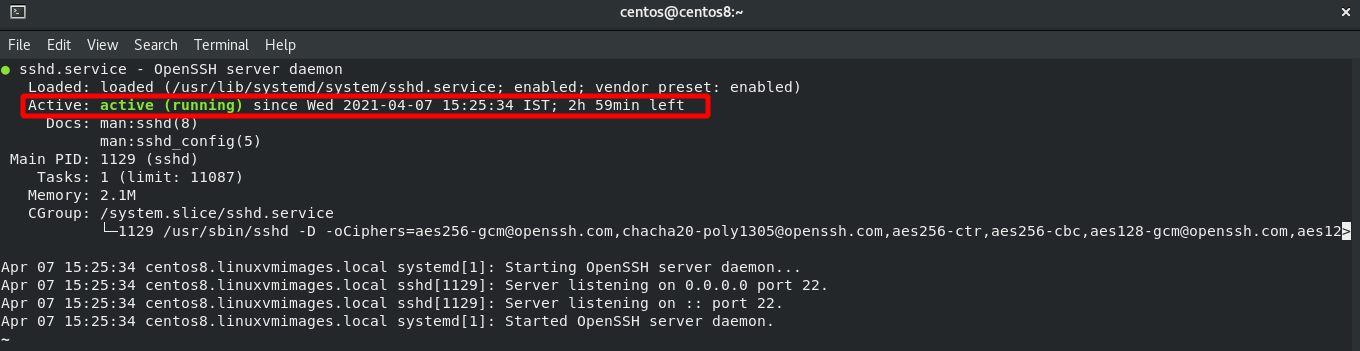
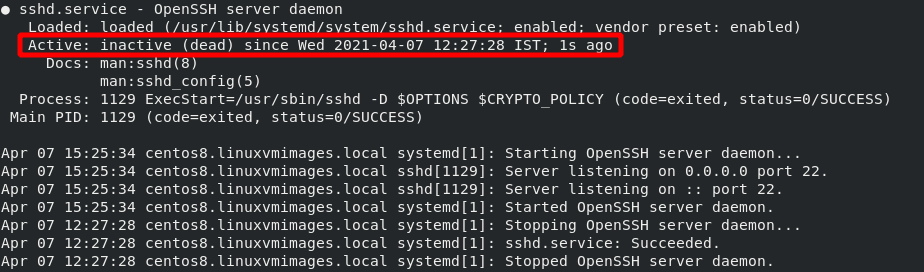
The above command should report if the service is running or not, as shown in the screenshots below.
Solution
To resolve SSH issues caused by the service not running, use the system to start the service. If the service responds with errors, check the logs and fix the issues reported in the log.
Use the command below to check the service logs.
Use the command below to start or stop the SSH service using systemd.
Issue 2: SSH on Non-Standard Port
The second common issue when debugging SSH connections is the use of a non-standard port. If SSH is running on another port other than the default port 22, you will not connect to the remote host unless you explicitly specify the port on which SSH is running.
To view the port on which SSH is running, use a tool such as netstat as below:
tcp 0 0 0.0.0.0:56 0.0.0.0:* LISTEN 1131/sshd
tcp6 0 0 :::56 :::* LISTEN 1131/sshd
The above output shows which port the SSH service is running on. In this case, it is port 56.
Solution
To resolve this issue, you can use the information from netstat to explicitly specify the port in your ssh command as:
Issue 3: Another Service using the same port
Another cause of SSH connection errors is if another service or process also uses the same port as the SSH service. For example, if SSH is explicitly specified to run on port 80 (terrible idea), a service like Apache may be using the same port.
To view if another process is using the same port as SSH, check the logs using the command:
This command should return an error like the one shown below, indicating if another process uses the SSH-bound port.
It is good to ensure that the port binding error is caused by another service, not security measures such as SELinux.
Solution
There are various ways you can use to resolve this issue. These include:
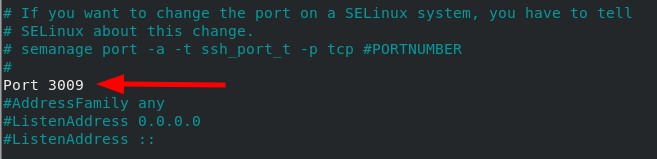
The first is to bind the SSH service to a different port. You can do this by editing the SSH config file. For example, change Port entry to port 3009 as shown in the commands:
Port 3009
Another method you can use to resolve this issue is to stop the service using the SSH port. For example, stop apache service using port 80 as:
sudo systemctl disable httpd
Issue 4: Firewall
If you have tried all the above methods and still no SSH connection, you can move on to the next possible cause of the issue: Firewall restrictions. Depending on the Firewall method you are using (UFW or Iptables), you need to ensure that the firewall allows SSH connections.
Solution
Firewall rules are wide and can vary depending on the system configuration. Thus, I cannot cover every aspect. However, the following is a simple solution to ensure the SSH service is allowed on UFW Firewall.
You can also reset all the UFW rules and start over. That will allow you to troubleshoot the firewall connections from scratch.
Issue 5: Disabled Password Logins
Sometimes you can configure SSH not to accept password logins and only use public-key authentication. That can cause an issue if the public key is not available on the server or missing your private key pair.
To check if password logins are allowed, cat the ssh config as:
#PasswordAuthentication yes
PasswordAuthentication yes
# PasswordAuthentication. Depending on your PAM configuration,
# PAM authentication, then enable this but set PasswordAuthentication
The above output shows that password logins are allowed.
Solution
To resolve the above issue, you can use two methods:
First, if you have the value set to no, change the PasswordAuthentication value to yes and restart the ssh service.
The other method is to create an ssh key-value pair and use it to log in to the server. To learn how to create ssh key-value pair, use the following guide.
https://linuxhint.com/find-ssh-public-key/
https://linuxhint.com/use-ssh-copy-id-command/
Conclusion
In this quick guide, we discussed major causes of SSH connection errors and how you can resolve them. Although this guide covers common issues, you may find errors specific to your system based on the configuration and permissions.