“A username and password for a single account are the primary requirements for accessing a Linux system. In order to verify a user during a system login attempt, all user accounts passwords are saved in a file or database. Finding this file on a user’s machine is beyond the knowledge and abilities of every user. Linux checks the password given by the user against an entry in one or more files located in the directory named “/etc.” when the user logs in with a username and password.
All the crucial data required for user login is stored in the /etc/passwd files. The user’s account information is kept in the /etc/passwd file, to put it another way. The entire list of users on your Linux system is contained in this plain text file. It contains data about the user name, password, group ID, user id, shell, and home directory. Only superuser or root user accounts should have restricted write access permissions.”
This article will show you where and how to save the passwords for system user accounts on Linux distributions.
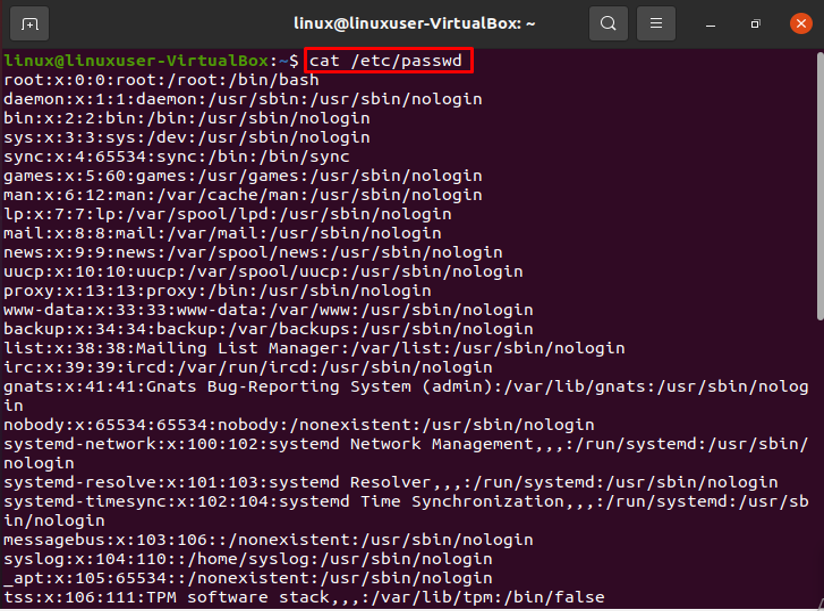
Examining the /etc/passwd File
In order to run administrative commands, you must have root access. The details of your system’s user account are in the /etc/passwd file. The colon “:” symbol separates each stored field. The following command will display each entry in the /etc/passwd file:
The command mentioned above will list every user on your Linux system, and hence terminal’s screen will show the following format:
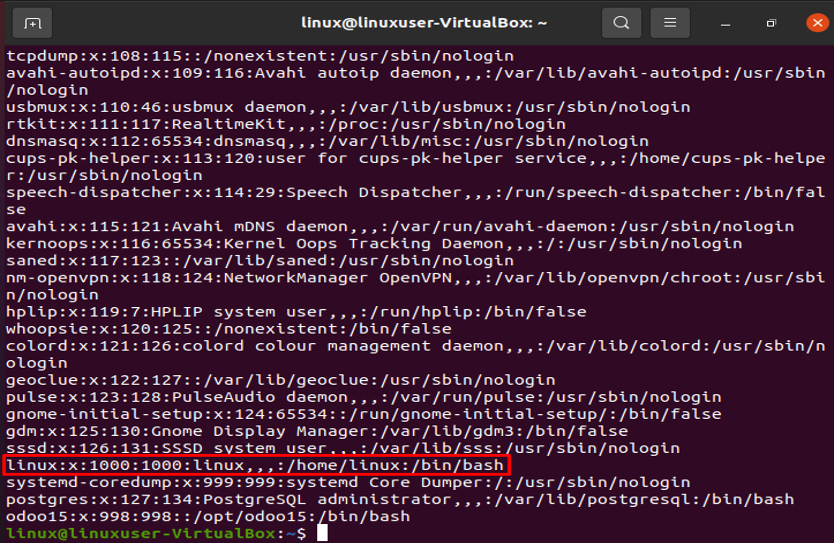
The information about the currently used account is shown in the highlighted portion below.
There are several fields of data divided by colons (:).
Linux: Username is shown in field one. The username field can only have between 1 and 32 characters. Linux is the username in the sample above.
Password (x): The “x” character denotes the encrypted password, as can be seen in the aforementioned example.
UID (1000): Each user must have their own unique user ID. The user ID in the aforementioned screenshot is 1000.
GID (1000): The group ID is represented by the following field. The GID is kept in the file /etc/group. The example indicates that the user is a member of group 1000.
Details (linux): Comments should go in the field below. You can enter further details about the identified person in this box, such as the individual’s complete name, contact information, etc. The user does not offer a phone number in the case above, though.
Home directory (/home/linux): The location of the user’s current home directory is displayed in this field. It will show “/” if the requested directory does not exist.
/bin/bash shell: /bin/bash is the default absolute path for a shell or command.
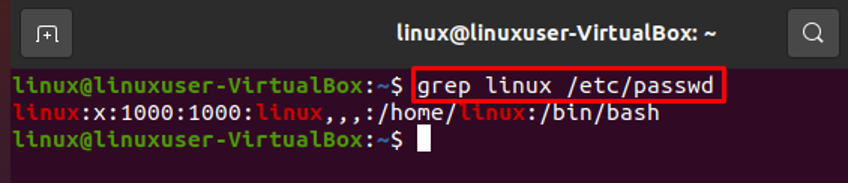
Searching User in the /etc/passwd File
A specific user can be found easily by using the grep command. For instance, if we wish to search for the username “linux” in the /etc/passwd file, we may quickly do it by using the following command, which will save us time:
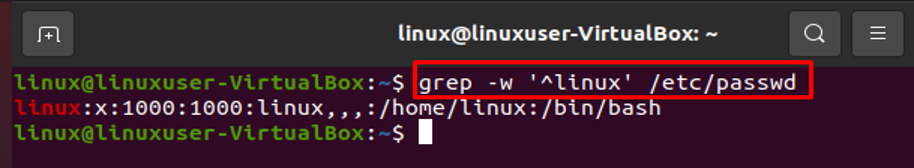
In this regard, we can also use the following command:
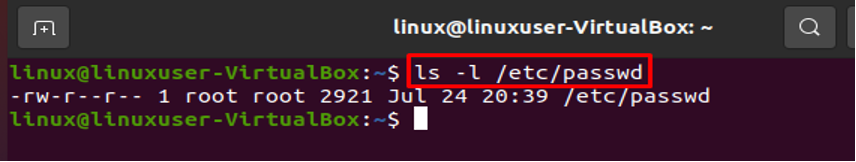
View the /etc/passwd File’s Permissions
As we stated above, the /etc/passwd file must have the owner be superuser or root, and all users other than root should have read rights.
To check the read rights on the file, type the following:
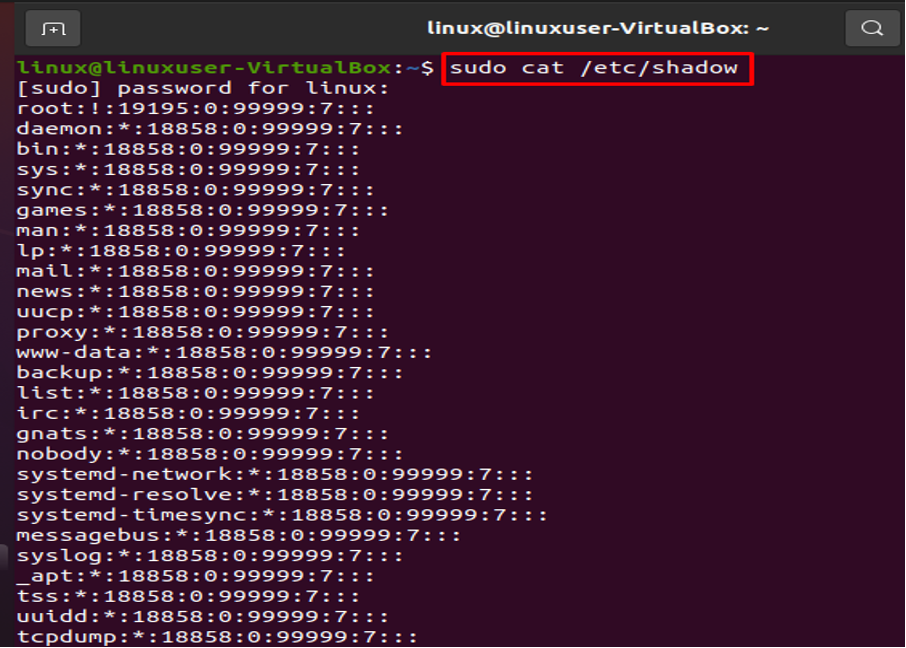
Examine the File /etc/shadow
Your whole encrypted password collection is stored in the root-only /etc/shadow file. Every password is viewable in encrypted form. Let’s execute the next command to show the content:
Conclusion
The aforementioned article demonstrates that the Linux operating system keeps all user account details and passwords in the /etc/passwd file. Additionally, we have seen every encrypted password kept in the /etc/shadow file. To learn more about the user’s group, you can also look through the /etc/group file.