Nmap is very useful. Some of the characteristics of Nmap are:
- Nmap is powerful and can be used to scan vast and huge networks of various machines
- Nmap is portable in a way that supports several operating systems such as FreeBSD, Windows, Mac OS X, NetBSD, Linux, and many more
- Nmap can support many techniques for network mapping that include detection of OS, a port scanning mechanism, and version detection. Thus it is Flexible
- Nmap is easy to use as it includes the more enhanced feature and can start with simply mentioning the “nmap -v-A target host”. It covers both the GUI and the command-line interface
- Nmap is very popular as it can be downloaded by hundreds to thousands of people every day because it is available with a variety of OS such as Redhat Linux, Gentoo, and Debian Linux, etc.
The key purpose of Nmap is to make the internet secure for users. It is also available free of cost. In the Nmap package, some important tools are involved that are uping, ncat, nmap, and ndiff. In this article, we will start by doing the basic scan on a target.
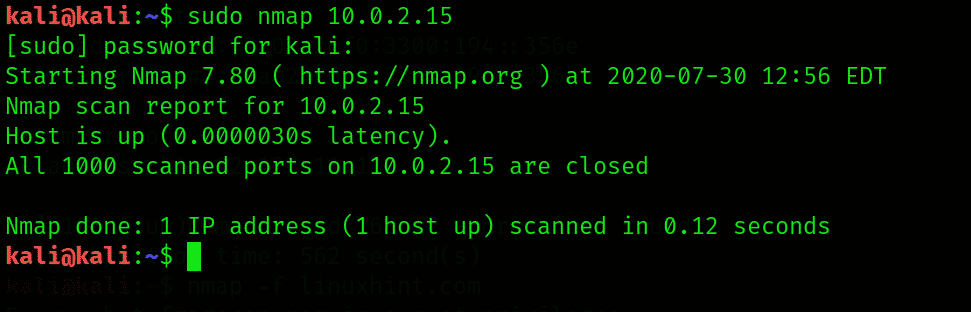
In the first step, open a new terminal and write the following syntax: nmap <target IP or hostname>. Then scan the website that will allow you to perform the scan. Here we will use the following command
By noticing the output, Nmap can recognize the open ports, like if they are UDP or TCP, can also search for IP addresses and determine the application layer protocol. For better exploiting the threats, it is essential to identify the various services and the open ports of the target.
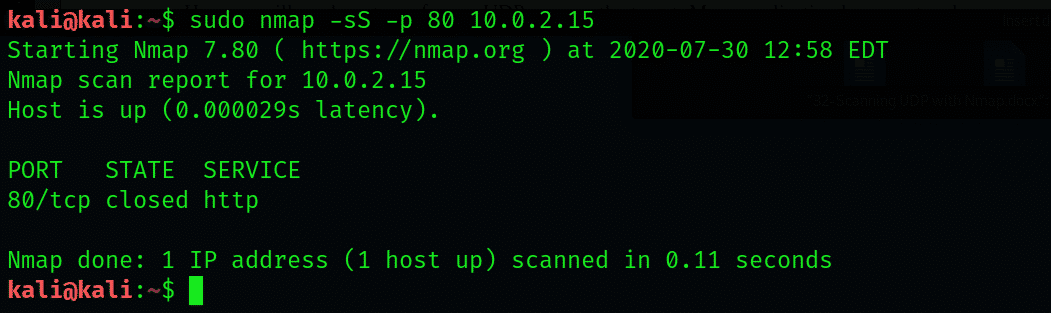
By using Nmap, performing a stealth scan
On an open port, initially, the Nmap creates a TCP three-way handshake. Once the handshake is established, then all the messages are exchanged. By developing such a system, we will become known to the target. Hence, a stealth scan is performed while using the Nmap. It will not create a complete TCP handshake. In this process, firstly, the target is tricked by the attacker device when a TCP SYN packet is sent to the specific port if it is open. In the second step, the packet is sent back to the attacker device. At last, the TCP RST packet is sent by the attacker for resetting the connection on the target.
Let us see an example in which we will examine the port 80 on the Metasploitable VM with Nmap using the stealth scan. The –s operator is used for stealth scan, -p operator is used to scanning a particular port. The following nmap command is executed:
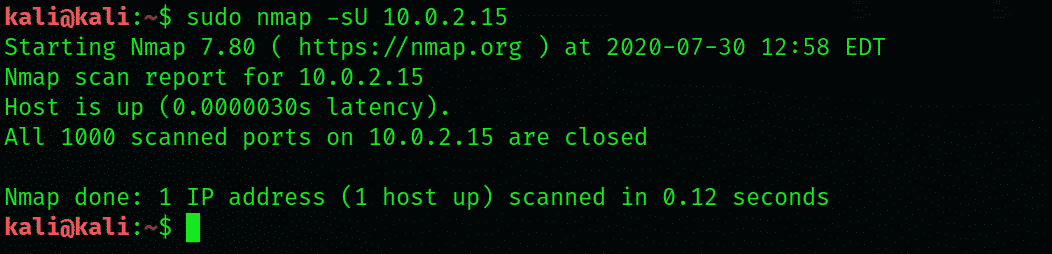
By using Nmap, scanning the UDP ports
Here we will see how to perform a UDP scan on the target. Many application layer protocols have UDP as a transport protocol. The –sU operator is used to carrying out the UDP port scan on a particular target. This can be done by using the following syntax:
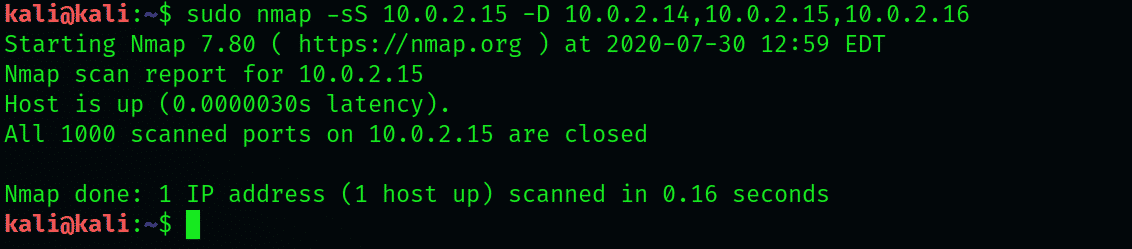
Detection evading using Nmap
IP addresses are included in the header of the packet when a packet is sent from one device to the other. Similarly, the source IP addresses are included in all packets while carrying out the network scan on the target. Nmap also uses the decoys that will trick the target in a way that it seems arising from multiple sources IP addresses instead of the single one. For decoys, -D operator is used along with the random IP addresses.
Here we will take an example. Suppose we want to scan the 10.10.10.100 IP address, then we will set three decoys like 10.10.10.14, 10.10.10.15, 10.10.10.19. For this, the following command is used:
From the above output, we noticed that the packets have decoys, and source IP addresses are used during the port scan on the target.
Firewalls evading by using Nmap
Many organizations or enterprises contain the firewall software on their network infrastructure. The firewalls will stop the network scan, which will become a challenge for the penetration testers. Several operators are used in Nmap for the firewall evading:
-f (for fragmenting the packets)
–mtu (used for specifying the custom maximum transmission unit)
-D RND: (10 for creating the ten random decoys)
–source-port (used to spoof the source port)
Conclusion:
In this article, I have shown you how to perform a UDP scan using Nmap tool in Kali Linux 2020. I have also explained all the details and necessary keywords used in the Nmap tool.