SSL certificates have the same encryption level as trusted CA-signed SSL certificates. Using openssl, you can generate a self-signed SSL certificate in the Linux command line with just a few steps. This guide looks at creating a self-signed SSL certificate on Linux.
How to Create a Self-Signed SSL Certificate on the Linux Command Line
Generating your certificate on the Linux command line and signing it using the private key is easy. Here, we can create our SSL certificate by following a few steps using the terminal.
Install the OpenSSL on Linux
OpenSSL is an open-source command-line tool that allows you to perform various tasks related to SSL. This tool is also required to generate the self-signed SSL certificates, which you can easily install with the help of Linux repositories. You can install it through the following commands:
sudo apt update
sudo apt install openssl -y (for Debian-based distros)
sudo pacman -Sy openssl (for Arch Linux)
sudo dnf install openssl (for RPM-based distros)
Create a Self-Signed Certificate
After successfully installing the OpenSSL, you can generate an SSL certificate using just one command. OpenSSL creates the certificate and associated encryption key in the current directory. Hence, please open the specific directory where you want to create the key or certificate. Here, we create a self-signed SSL certificate named “sample” using the following command:
Let’s try to understand the previous command better by breaking it:
The system asks you with questions which are related to that organization to process the intended certificate.
Note: You can use any value other than the common name field to use the certificate for testing or personal development. Moreover, you need to enter the website’s domain that installed the certificate.
Bonus Tip: If you want your private key to be encrypted, remove the -nodes option from the previous command.
Read the Content of the Self-Signed SSL Certificate
You can check the location of the newly created certificates and private keys through the ls command. Since we created a file named “sample”, we should find that file and its private key under the directory.
The created certificate is PEM-formatted. Run the following command in a terminal to read its contents:
We included the following in the previous command:
| -noout | Escapes the encoded version of the certificate. |
| -in | Specifies the file containing the certificate. |
| -text | Prints the certificate output in text form. |
Conversely, use the -x509 command with the -pubkey option to extract the public key from the certificate. Hence, the certificate prints the public key in PEM format.
Generate the Self-Signed SSL Certificate with No Prompt
If you don’t want to be prompted to answer any questions when generating a self-signed SSL certificate, you can specify all subject information using the -subj option as follows:
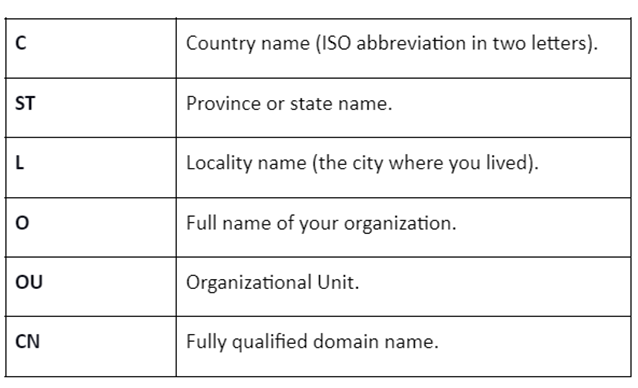
The list of fields that is specified under -subj is listed in the following:
Conclusion
A self-signed SSL certificate enables a secure connection for the web browser. This certificate acts like a certificate that is created by a trusted authority. For this reason, the SSL certificates are commonly used for home or company intranets for applications such as testing and development purposes.
This guide has everything you need to know to create a self-signed SSL certificate on the Linux command line through the openssl tool. For this, you need to provide the details about the certificate such as determining its validity, the key size, etc.