Components of Metasploit framework
Modules are indeed the Metasploit Framework’s primary components. Modules are independent bits of code or software that provide Metasploit with functionality. Exploits, Nops, posts, payloads, auxiliary, and encoders are the six basic modules.
Exploits
Exploit modules are computer programs stored in the database that allows the attacker to access the victim’s device when executed on a client machine. The attacker will attempt to compromise the payload module, including the Meterpreter shell, by exploiting a vulnerability on the local and remote system.
Nops
NOP stands for “No Operation in low-level programming” (assembly language). When a CPU stacks an instruction, it essentially does nothing for one cycle before progressing the register towards the next instruction.
Posts
These are all the post-exploitation modules that could be used on infected targets to obtain specific information such as evidence, pivot, and go further into a victim’s network and system. Penetration testers can use the Metasploit post exploits module to gather information from infected workstations, such as hashes, tokens, provide passwords, and much more.
Payloads
It is made up of code that is executed remotely. So, following exploitation, a code described as the payload is executed, which may be thought of as a second process that assists in taking control of the system and performing additional activities. The payload is a collection of guidelines that the victim’s machine will execute once it has been compromised. Payloads can be as simple as a few lines of code or as complex as small apps like the Meterpreter shell. Around 200 payloads are included in Metasploit.
Auxiliary
In comparison to exploits, it is unique. It can be used for port scanning, sniffing, and DOS attacks, among other things. Auxiliary modules, except exploit modules, do not involve using a payload to run. Scanners and SQL injection tools are all examples of these types of modules. Penetration testers use the auxiliary directory’s variety of scanners to gain a thorough overview of the attack system before moving on to exploit modules.
Encoders
The transmission protocol or the end application may be sensitive to “bad characters,” which might cause your shellcode to break in various ways. The majority of problematic characters can be eliminated by encrypting the payload.
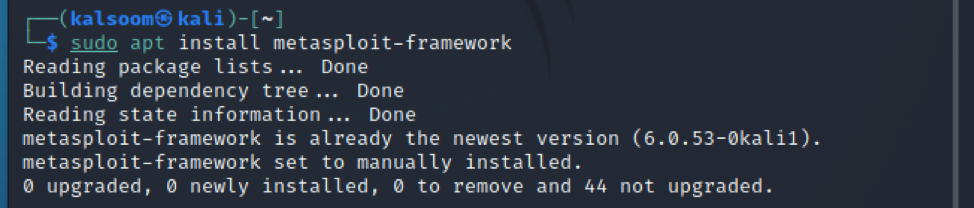
Installation of Metasploit framework in Kali Linux
In this article, we are using Kali Linux for some basic understanding of the Metasploit framework. So we can install it in kali with the help of the following prescribed command:
Importanat Command of Metasploit
You will want to access your Metasploit console once you have installed your testing tools. Simply run msfconsole from the CLI to start the MSFconsole. It is used to access Metasploit’s interface. It will seem as follows:
It takes some time to become used to the CLI, but it is easy to use once you are there. MsfConsole is perhaps the only means to access all of Metasploit’s functionality. Tab completion is also available in MsfConsole for popular commands. Making yourself comfortable with the MsfConsole is a crucial step on your path to becoming a Metasploit expert.
To get a list of Metasploit commands and associated descriptions, type “help” into the terminal. This is how it should look:
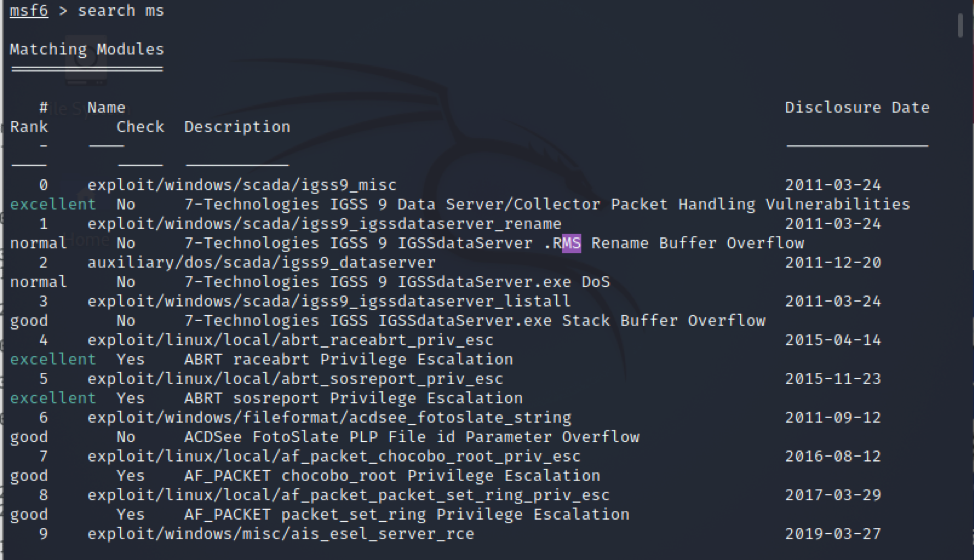
This command is used to search the MSF for payloads, exploits, auxiliary, and other items. Let’s look for Microsoft exploits by typing “search ms” into the search box.
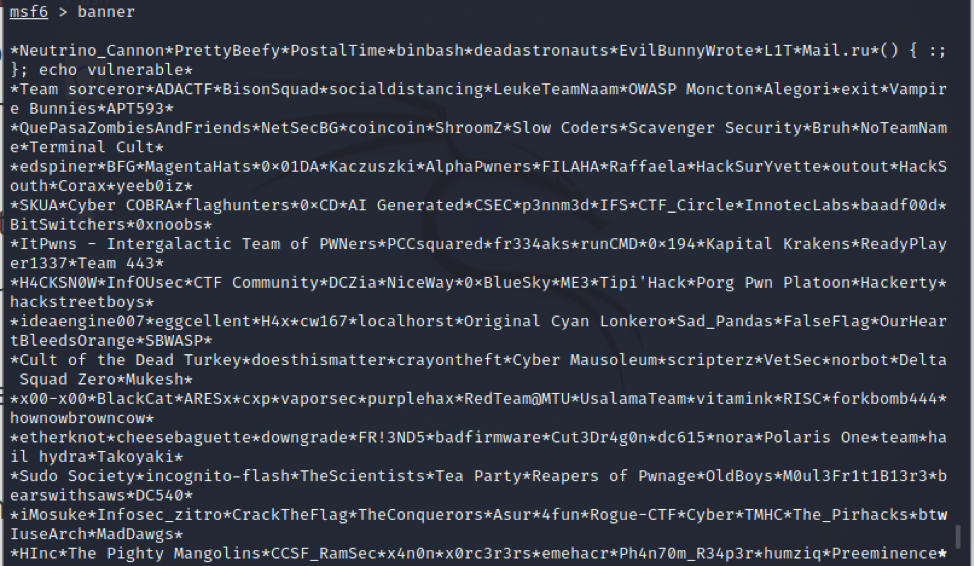
It displays a banner that is created randomly, run the prescribed command as:
Use the “use” command to choose a specific module once you have decided the one you want to use. The use command switches the context to a certain module, allowing you to use type-specific commands.
Conclusion
Metasploit offers a set of tools that may be used to conduct a full information security audit. The vulnerabilities reported in the Common Security flaws and Exploits database are routinely updated in Metasploit. This guide covered almost all important concepts related to Metasploit. A brief overview, Metasploit components, its installation in Kali Linux, and some of the important commands of the Metasploit framework are discussed here.